
Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

Application platform modernization is pushing cloud security teams to increasingly support infrastructure teams in new ways as they adopt new cloud architectures. One avenue that is gaining steam is the use of serverless container environments, often described as serverless containers or container-as-a-service (CaaS).
AWS Fargate, which allows developers to run containerized workloads without managing the underlying compute infrastructure, is an example of this.
Sysdig now extends its runtime malware detection capabilities to AWS Fargate environments, enabling SOC and CSIRT teams to maintain runtime malware detection coverage while workloads run in fully managed container services.
This operational model can simplify infrastructure management, improve scalability, and allow development teams to focus on building and deploying applications rather than maintaining servers. Platform teams can also benefit from faster deployment cycles and reduced operational overhead.
But for SOC and CSIRT teams, this architectural shift introduces a new operational consideration. As organizations move workloads to AWS Fargate, analysts need to ensure that runtime security visibility and malware detection coverage remain consistent with what is applied across other containerized environments.
Why AWS Fargate still requires runtime security
It's easy to assume that fully managed container services like AWS Fargate would reduce the risk of malware because of their different operational model. There is no underlying host to manage, no traditional host-based agent deployment model, and less direct visibility into runtime activity than in self-managed container environments.
However, malware remains a risk that security teams must address.
Containers running in AWS Fargate still execute application code, access cloud services, and interact with sensitive data. Similar to other containerized environments, if attackers compromise an application they can introduce malicious processes, deploy cryptominers, or execute compromised container images inside running tasks.
For defenders responsible for detecting runtime threats in AWS Fargate, the challenge becomes maintaining visibility into workloads even when infrastructure management responsibilities are handled by the platform.
Runtime visibility challenges in serverless environments
Traditional container security strategies typically rely on host-level instrumentation, infrastructure monitoring, and static scanning of container images. These approaches work well when teams have complete control of their Kubernetes nodes or virtual machines running their container infrastructure.
AWS Fargate introduces a different operational model for how container workloads are deployed and managed. Cloud security teams cannot deploy host-level agents or rely on the same infrastructure-level access available in self-managed environments. This can create concerns that adopting serverless containers may reduce visibility into runtime threats such as malware.
At the same time, the types of threats security teams monitor remain consistent across container environments. Malware can still be introduced into container environments through compromise, vulnerabilities, manipulated container images, or exploited application services.
Attackers can deploy malicious binaries, execute unauthorized processes, or run cryptomining software inside container workloads. Runtime detection capabilities help security teams investigate these activities and support compliance requirements.
Extending runtime malware detection to AWS Fargate
To support organizations adopting serverless container architectures, Sysdig is introducing runtime malware detection support for AWS Fargate. This capability allows security teams to extend malware detection capabilities into their serverless environment.
With this release, organizations running containers in AWS Fargate can maintain malware detection coverage while continuing to use the same investigation and response workflows.
This functionality builds on Sysdig malware detection capabilities trusted in containerized host and cloud environments.
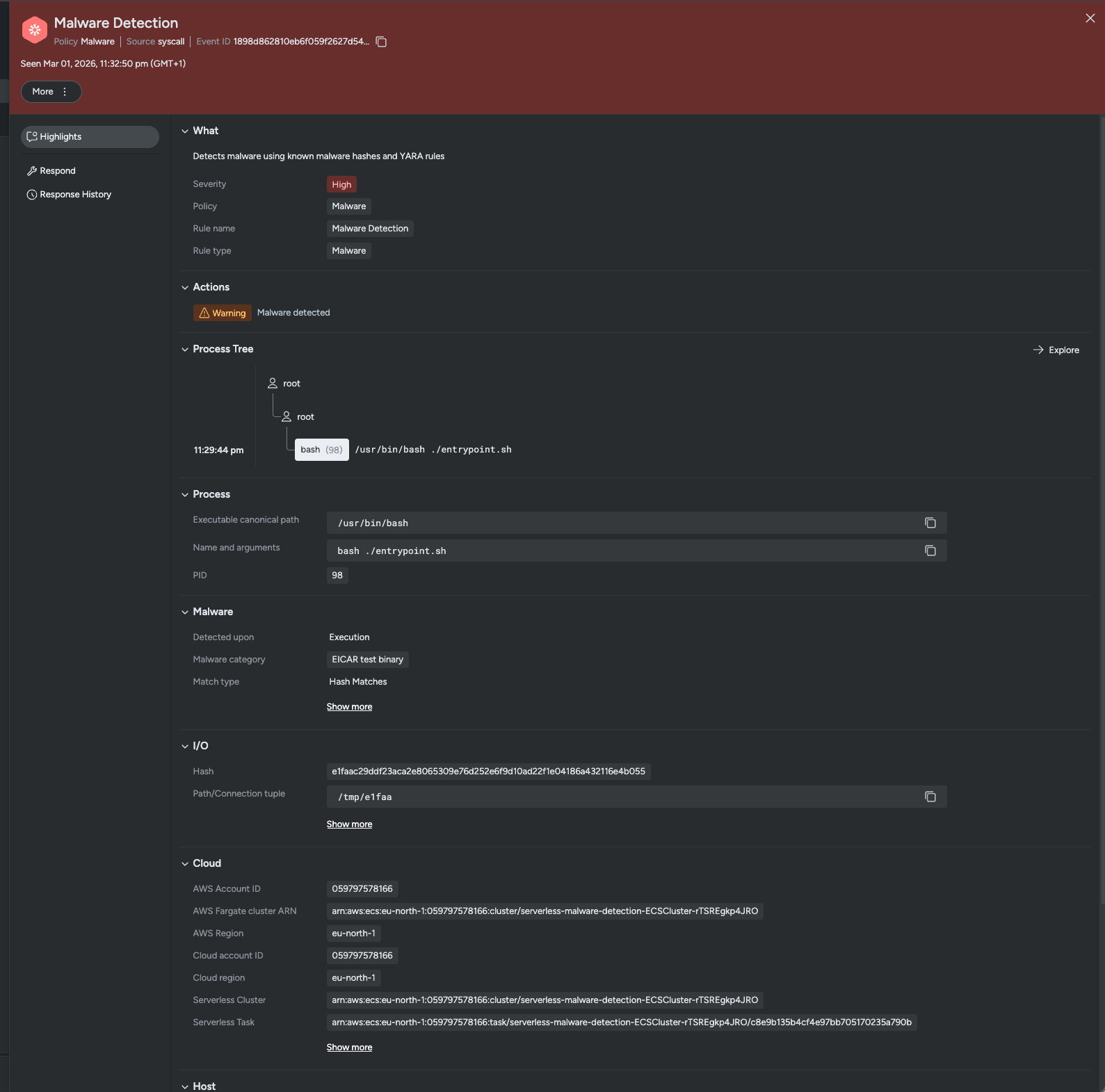
In the scenario above, an analyst would see an alert triggered through Malware Hash Detection.The system identifies the EICAR Anti-Virus Test File, an industry-standard file used to test and verify the detection efficacy of security programs. While this specific instance utilizes the EICAR file as an academic exercise to validate the detection, the underlying technology is the same used to neutralize real-world threats. Whether the threat in question is a known ransomware variant or a sophisticated cryptominer, Sysdig’s Malware Hash Detection ensures that if the signature is known, the threat is detected.
Detecting malware during runtime execution
Preventative container security controls often rely on scanning container images during the build process. Image scanning remains an important preventative control, but it falls short of detecting threats at runtime.
Sysdig malware detection focuses on identifying malicious activity during workload execution.
Malware can be detected when malicious binaries are written to the container filesystem, or when suspicious processes attempt to execute. This allows analysts to detect threats based on runtime behavior.
Runtime detection provides visibility into malware that may bypass preventative controls earlier in the software lifecycle. If a malicious binary is introduced into a container after deployment, runtime detection can still identify the activity.
For SOC and CSIRT teams, this means alerts are generated based on active runtime behavior. Analysts can investigate suspicious execution attempts, determine the scope of activity, and respond to threats before they spread to other services.
Consistent security across Kubernetes and AWS Fargate
Most modern organizations operate multiple compute platforms simultaneously. A typical environment may include Kubernetes clusters, self-managed container environments, traditional virtual machines, and serverless container services like AWS Fargate. Security analysts need consistent protection across all of these environments.
Sysdig extends malware detection and runtime protection into Fargate environments, enabling defenders to detect malicious execution attempts even in fully managed container runtimes. This helps maintain runtime protection across Kubernetes clusters, self-managed containers, and AWS Fargate.
With Sysdig, SOC teams can investigate threats using familiar workflows, regardless of where the workload is running.
Supporting cloud modernization without losing compliance coverage
For CISOs and security leaders, infrastructure modernization often involves balancing operational efficiency with security and compliance requirements.
Platform teams adopt AWS Fargate to accelerate development and reduce infrastructure management overhead. Security leaders must ensure that these architectural decisions do not reduce security visibility or introduce compliance gaps.
By extending runtime malware detection into AWS Fargate environments, Sysdig helps organizations support platform modernization while maintaining consistent runtime security controls. Analysts can continue detecting malware and suspicious execution attempts while infrastructure teams adopt serverless container platforms.
This alignment allows organizations to modernize their application platforms without sacrificing runtime security visibility and detection coverage.
Runtime security that evolves with cloud architecture
AWS Fargate represents an important evolution in cloud application deployment. By removing infrastructure management responsibilities, it allows organizations to deploy and scale containerized applications more efficiently.
However, removing infrastructure management does not remove the need for runtime threat detection. Security visibility must evolve alongside cloud architecture.
By extending runtime malware detection into AWS Fargate environments, Sysdig enables SOC and CSIRT teams to maintain detection coverage across modern cloud environments. Cloud security teams retain the ability to detect malicious execution attempts, investigate runtime activity, and respond to threats across Kubernetes clusters, traditional container platforms, and AWS Fargate workloads.
With Sysdig, organizations can adopt modern serverless container architectures while maintaining strong runtime malware detection and cloud security visibility.

