blogs
Insights at Cloud Speed
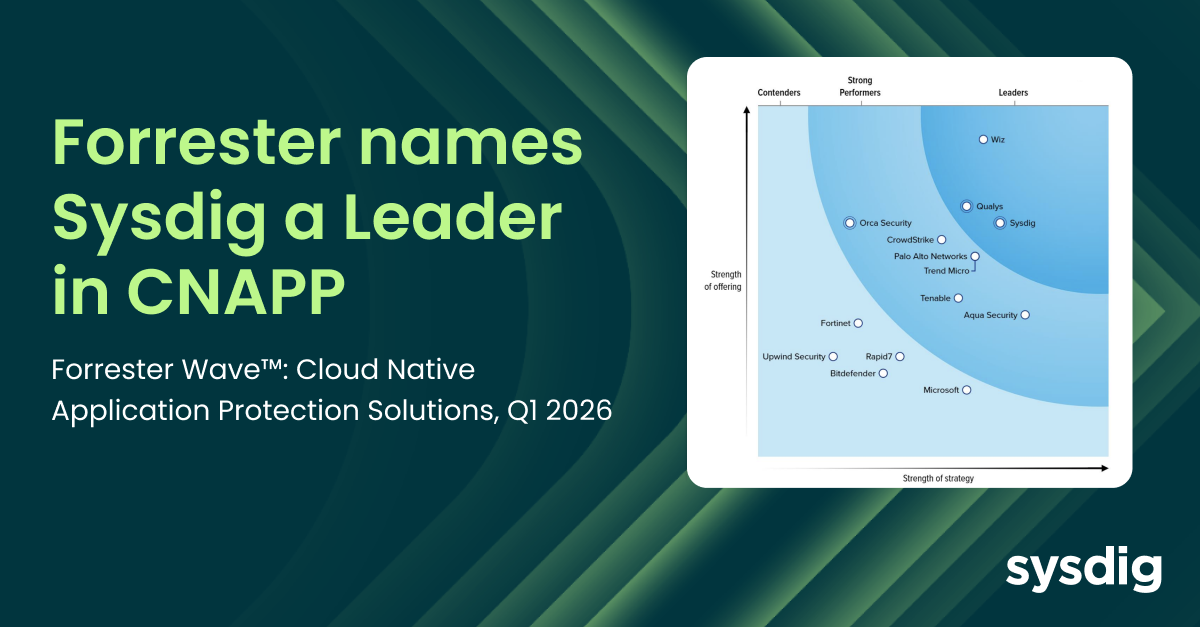
Sysdig named a Leader in the Forrester Wave™: Cloud Native Application Protection Solutions, Q1 2026
Matt Kim
|
February 17, 2026
Sysdig named a Leader in the Forrester Wave™: Cloud Native Application Protection Solutions, Q1 2026

AI-assisted cloud intrusion achieves admin access in 8 minutes
Alessandro Brucato
|
February 3, 2026
AI-assisted cloud intrusion achieves admin access in 8 minutes
Securing GPU-accelerated AI workloads in Oracle Kubernetes Engine
Manuel Boira
|
February 2, 2026
Securing GPU-accelerated AI workloads in Oracle Kubernetes Engine

Our customers have spoken: Sysdig rated a Strong Performer in Gartner® Voice of the Customer for Cloud-Native Application Protection Platforms
Marla Rosner
|
January 22, 2026
Our customers have spoken: Sysdig rated a Strong Performer in Gartner® Voice of the Customer for Cloud-Native Application Protection Platforms
join our newsletter
Stay up to date– subscribe to get blog updates now
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
Detecting and Mitigating the “tj-actions/changed-files” Supply Chain Attack (CVE-2025-30066)
March 15, 2025
Michael Clark
Detecting and Mitigating the “tj-actions/changed-files” Supply Chain Attack (CVE-2025-30066)
Open Source
Threat Research
Detecting CVE-2025-22224 with Falco
March 13, 2025
Nigel Douglas
Detecting CVE-2025-22224 with Falco
Cloud Security
Kubernetes & Container Security
2025 is cloud security’s breakthrough year
March 12, 2025
Crystal Morin
2025 is cloud security’s breakthrough year
Cloud Security
Threat Research

From Risk to ROI: Making Security Insights Matter to Business Leaders
March 6, 2025
Zain Ghani
From Risk to ROI: Making Security Insights Matter to Business Leaders
Cloud Security
In-use vulnerability prioritization
March 4, 2025
Matt Kim
In-use vulnerability prioritization
Cloud Security
Inline response actions: Streamlining incident response in the cloud
February 27, 2025
Paolo Polidori
Inline response actions: Streamlining incident response in the cloud
Sysdig Features
