blogs
Insights at Cloud Speed
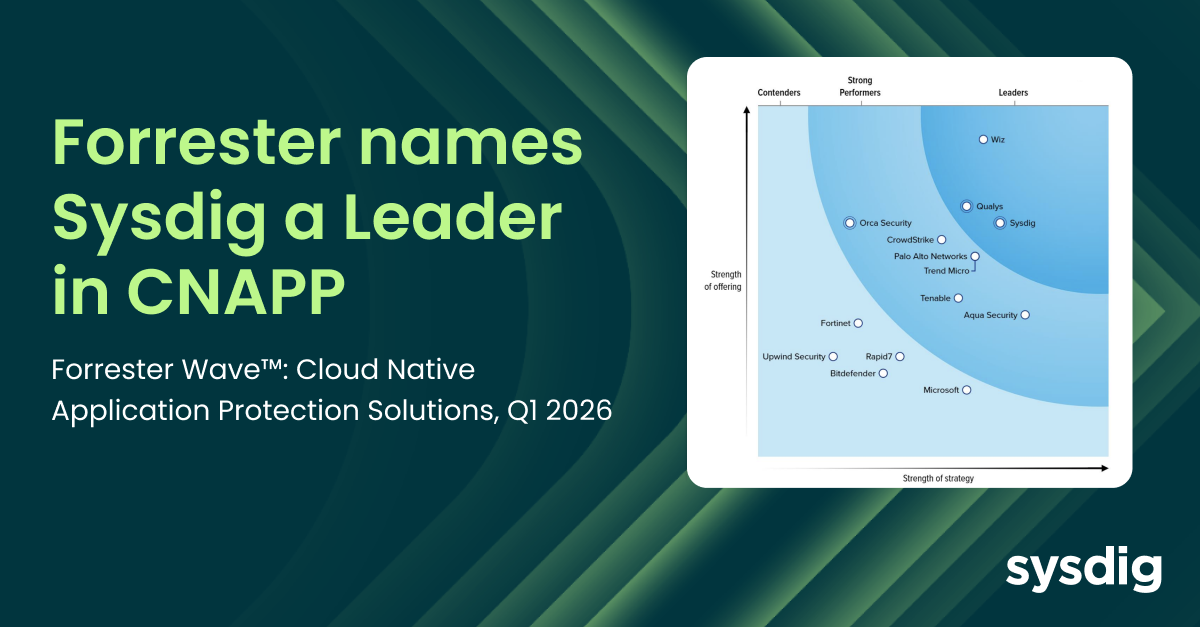
Sysdig named a Leader in the Forrester Wave™: Cloud Native Application Protection Solutions, Q1 2026
Matt Kim
|
February 17, 2026
Sysdig named a Leader in the Forrester Wave™: Cloud Native Application Protection Solutions, Q1 2026

AI-assisted cloud intrusion achieves admin access in 8 minutes
Alessandro Brucato
|
February 3, 2026
AI-assisted cloud intrusion achieves admin access in 8 minutes
Securing GPU-accelerated AI workloads in Oracle Kubernetes Engine
Manuel Boira
|
February 2, 2026
Securing GPU-accelerated AI workloads in Oracle Kubernetes Engine

Our customers have spoken: Sysdig rated a Strong Performer in Gartner® Voice of the Customer for Cloud-Native Application Protection Platforms
Marla Rosner
|
January 22, 2026
Our customers have spoken: Sysdig rated a Strong Performer in Gartner® Voice of the Customer for Cloud-Native Application Protection Platforms
join our newsletter
Stay up to date– subscribe to get blog updates now
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
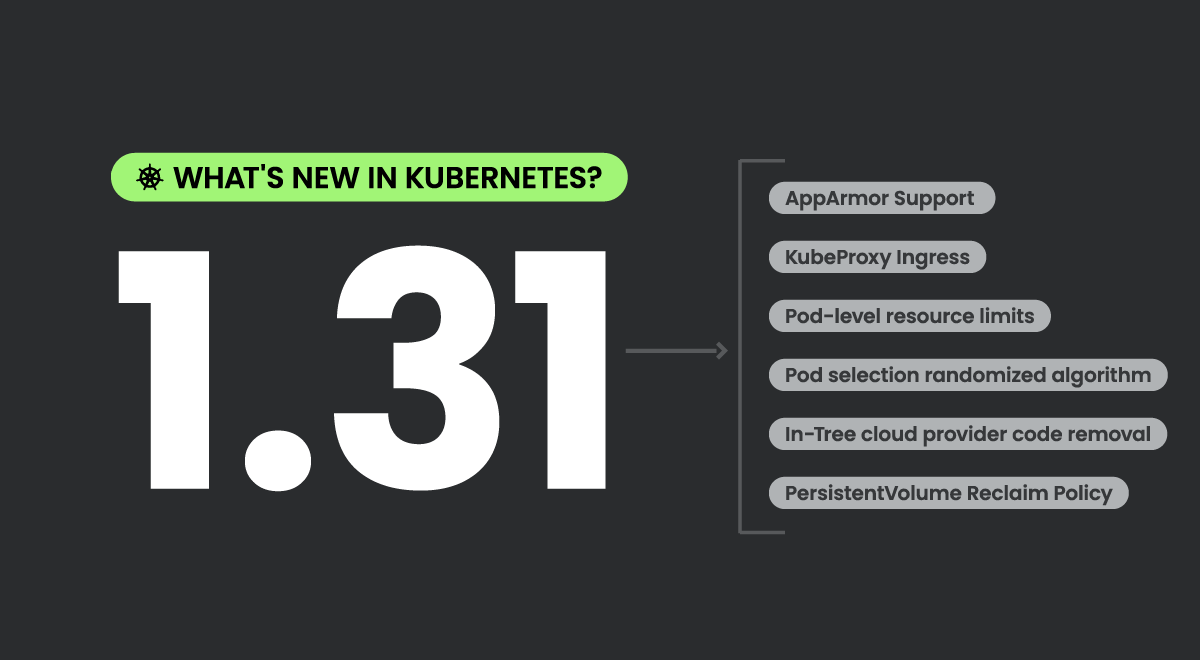
Kubernetes 1.31 – What’s new?
July 26, 2024
Nigel Douglas
Kubernetes 1.31 – What’s new?
Kubernetes & Container Security
2024 Gartner® CNAPP Market Guide: Runtime insights is a core pillar of cloud-native application protection platforms
July 26, 2024
Chris Petty
2024 Gartner® CNAPP Market Guide: Runtime insights is a core pillar of cloud-native application protection platforms
Cloud Security
Transforming enterprise data from leaky sieve to Fort Knox
July 25, 2024
Crystal Morin
Transforming enterprise data from leaky sieve to Fort Knox
Cloud Security
Compliance

SANS Cloud-Native Application Protection Platforms (CNAPP) Buyers Guide
July 25, 2024
Matt Kim
SANS Cloud-Native Application Protection Platforms (CNAPP) Buyers Guide
Cloud Security
Kubernetes & Container Security
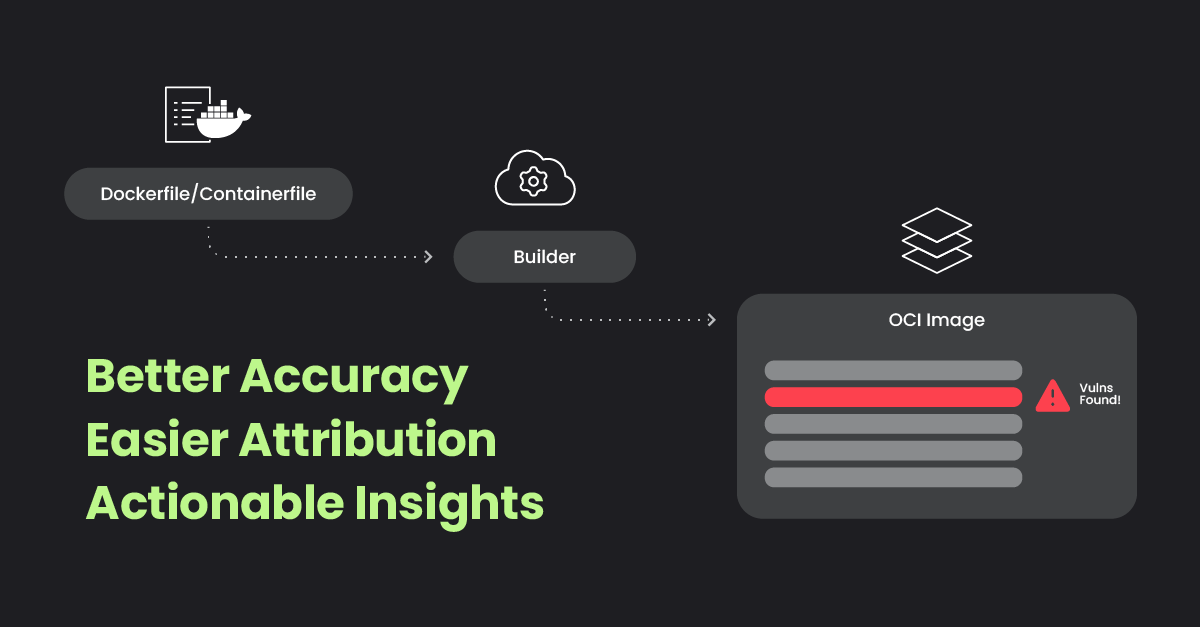
Introducing Layered Analysis for enhanced container security
July 23, 2024
Fede Barcelona
Introducing Layered Analysis for enhanced container security
Cloud Security
Kubernetes & Container Security
Sysdig Features
Sysdig Threat Research Team – Black Hat 2024
July 22, 2024
Stefano Chierici
Sysdig Threat Research Team – Black Hat 2024
Cloud Security
Threat Research
