blogs
Insights at Cloud Speed
EtherRAT dissected: How a React2Shell implant delivers 5 payloads through blockchain C2
Sysdig Threat Research Team
|
December 16, 2025
EtherRAT dissected: How a React2Shell implant delivers 5 payloads through blockchain C2
Introducing runtime file integrity monitoring and response with Sysdig FIM
Paolo Polidori
|
December 16, 2025
Introducing runtime file integrity monitoring and response with Sysdig FIM

EtherRAT: DPRK uses novel Ethereum implant in React2Shell attacks
Sysdig Threat Research Team
|
December 8, 2025
EtherRAT: DPRK uses novel Ethereum implant in React2Shell attacks
Detecting React2Shell: The maximum-severity RCE vulnerability affecting React Server Components and Next.js
Sysdig Threat Research Team
|
December 5, 2025
Detecting React2Shell: The maximum-severity RCE vulnerability affecting React Server Components and Next.js
join our newsletter
Stay up to date– subscribe to get blog updates now
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
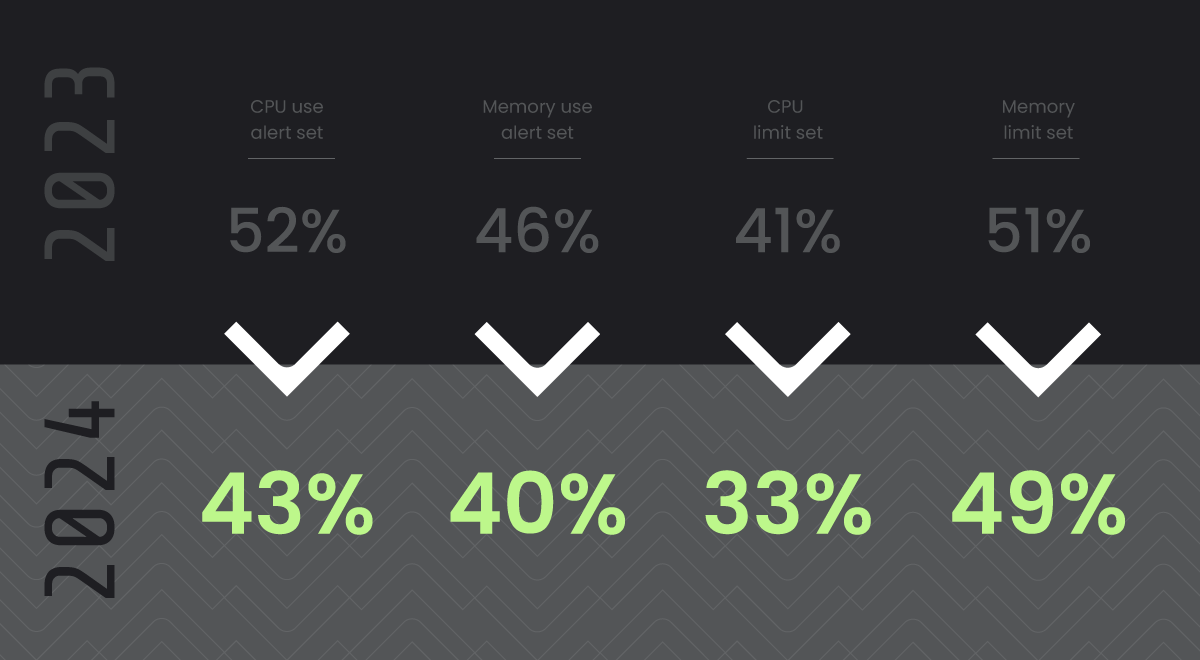
Resource Constraints in Kubernetes and Security
February 12, 2024
Nigel Douglas
Resource Constraints in Kubernetes and Security
No items found.
SBOM as a Core Element in Sysdig’s CNAPP Strategy for Enhanced Security
February 8, 2024
Joseph Yostos
SBOM as a Core Element in Sysdig’s CNAPP Strategy for Enhanced Security
No items found.

KuppingerCole Names Sysdig a Product and Innovation Leader for CNAPP
February 7, 2024
Marla Rosner
KuppingerCole Names Sysdig a Product and Innovation Leader for CNAPP
No items found.

How to secure your cloud credentials against AndroxGh0st
February 6, 2024
ashish chakrabortty
How to secure your cloud credentials against AndroxGh0st
No items found.
Cybersecurity in the Age of Regulation
February 5, 2024
Karen Walker
Cybersecurity in the Age of Regulation
Cloud Security

Kernel introspection from Linux to Windows
February 2, 2024
Nigel Douglas
Kernel introspection from Linux to Windows
No items found.