Events, webinars, and
workshops
.png)
Packets, Pods & Prompts: Why Open Source is the Future of Cloud Security
Join this exclusive conversation with three titans of open source—the minds behind Falco, Wireshark, and Kubernetes—as they explore why open-source models are not just resilient, but essential to the next wave of cloud security.
Kraken Discovery Labs
Looking to deepen your expertise in Kubernetes and cloud-native security? The Falco Kraken Discovery Labs virtual workshop provides participants the opportunity to experience the power of open source Falco firsthand. Run Atomic Red tests, then step into the Blue Team role to detect threats and create custom Falco detection rules. Whether you’re new to the field or an experienced Kubernetes threat detection engineer, you’ll discover how to leverage Falco to craft detection rules that extend MITRE ATT&CK coverage.

Get Hands-on with Sysdig for securing Google Cloud
Get Hands-on with Sysdig for securingGoogle CloudIn this lightweight hands-on interactive workshop, you’ll see how Sysdig helps Google Cloud users secure and accelerate innovation. Get insights into key cloud security use cases such as threat detection and response, vulnerability management & prioritization, posture management, and compliance.

Kraken Hunter
This is a half-day course focused on the challenges security professionals face in cloud native applications. In this hands-on class, you will go through various modules covering critical steps within the deployment lifecycle.Upon completion of the class you will have a better understanding of the eccentricities facing security professionals when dealing with cloud native applications as well as Sysdig and the OSS security tools leveraged in the greater ecosystem.
Secure DevOps with AWS and Sysdig
Join our AWS and Sysdig DevDay on Sysdig Secure for Cloud. In this hands-on workshop, you will learn how to use Sysdig’s Unified Vulnerability Scanning, CSPM, and Cloud Threat Detection to run cloud applications in production securely.
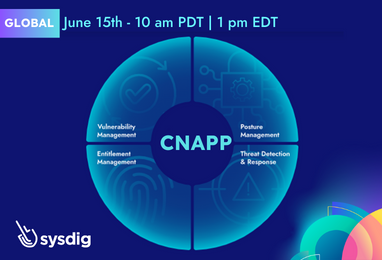
Shift Cloud Security Left and Right with CNAPP, Powered by Runtime Insights
Learn how to keep your security and DevOps teams shipping more secure applications by shifting security left and shielding right. Understand why real-time cloud detection and response across workloads, cloud services, and identities provides a fundamental CNAPP pillar to stop attacks and prevent breaches.
Cut Custom Metrics Cost by 75% and Observe More
Modern applications are increasingly being instrumented with “Custom Metrics” to monitor both their health and the impact on business.

Prioritize Cloud Risk and Accelerate Remediation with Sysdig and AWS
Join Sysdig and AWS for this interactive discussion and demo and learn how to achieve better cloud and container security through effective prioritization using runtime insights.






