Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

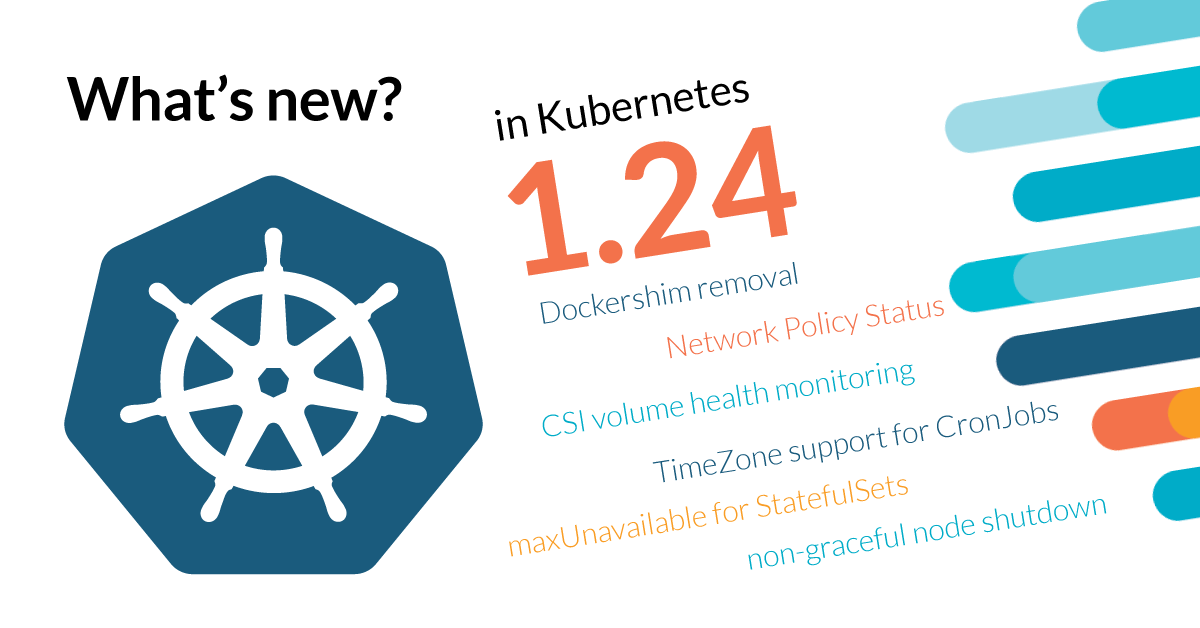
Kubernetes 1.24 is about to be released, and it comes packed with novelties! Where do we begin?
Update: Kubernetes 1.24 release date has been moved to May 3rd (from April 19th).
This release brings 46 enhancements, on par with the 50 in Kubernetes 1.23 and 56 in Kubernetes 1.22. Of those 46 enhancements, 14 are graduating to Stable, 15 are existing features that keep improving, and 17 are coming with innovative changes.
What makes this release different? Kubernetes 1.24 is a considerable milestone for two key reasons. First, dockershim, the Kubernetes Docker container runtime interface, is removed (as we already covered in a dedicated article). Second, StatefulSet and Deployment API v1beta1 are removed, accelerating the effort to move away from beta API versions.
This release brings exciting new features, many important deprecations, and some groundbreaking removals. Let's dive in!
What are the main topics discussed in this article?
We'll dive into the following topics:
- Dockershim removal
- API v1beta1 deprecations and removals
- Kubelet Credential Provider improvements
- Pod Security Standards enforcement
- Service API graduation to stable
- Storage enhancements
- Observability improvements
- And many more enhancements
Dockershim Removal – What you need to know
The removal of dockershim from Kubernetes 1.24 is a major milestone, marking the completion of the Kubernetes dockershim removal project, which started back in Kubernetes 1.20. Dockershim was the glue between Kubernetes and the Docker runtime, acting as a compatibility layer.
Before Kubernetes 1.24, you could run containers with Docker without using the containerd runtime. Now, you must explicitly use containerd or any other OCI-compliant container runtime (e.g., CRI-O, Kata Containers, etc.).
Check out our comprehensive guide on dockershim removal for more details about the implications of this change.
API v1beta1 deprecations and removals
Kubernetes 1.24 removes many v1beta1 API versions for various resource types. This is a continuation of the effort to deprecate beta API versions and encourage the use of stable v1 APIs.
The following APIs are being removed:
- autoscaling.k8s.io/v2beta1 (Horizontal Pod Autoscaler) - Migrate to autoscaling.k8s.io/v2 (stable)
- batch.k8s.io/v1beta1 (CronJob) - Migrate to batch.k8s.io/v1 (stable)
- discovery.k8s.io/v1beta1 (EndpointSlice) - Migrate to discovery.k8s.io/v1 (stable)
- policy.k8s.io/v1beta1 (Pod Disruption Budget) - Migrate to policy.k8s.io/v1 (stable)
- storage.k8s.io/v1beta1 (Storage Classes) - Migrate to storage.k8s.io/v1 (stable)
- Deployment, StatefulSet, DaemonSet, and ReplicaSet APIs v1beta1 - Migrate to apps.k8s.io/v1 (stable)
Kubelet Credential Provider
In Kubernetes 1.24, the Kubelet Credential Provider feature becomes generally available (GA). It allows kubelet to call external programs to dynamically retrieve credentials for image pulls. This is particularly useful for organizations that use dynamic credentials or time-limited tokens.
The Kubelet Credential Provider enables:
- Support for dynamic image pull credentials
- Rotation of image pull secrets without redeploying pods
- Integration with external credential management systems
Check out our article on kubelet features for more insights on kubelet improvements.
Pod Security Standards Enforcement
Pod Security Standards (PSS), which we covered in Kubernetes 1.22, are becoming more deeply integrated into Kubernetes.
In Kubernetes 1.24, Pod Security Standards are now considered stable. The restricted and baseline policies are now the preferred way to secure your pods.
The three tiers of Pod Security Standards are:
- Restricted: Enforcing the most restrictive policies
- Baseline: Preventing known privilege escalations
- Unrestricted: No restrictions
Service API Graduation to Stable
The Service API, which was introduced to provide a more flexible and powerful way to manage Kubernetes Services, is graduating to stable in Kubernetes 1.24.
This is great news for users who have been waiting for a more flexible Service API. The new Service API brings enhancements like:
- Better traffic management
- Improved routing capabilities
- Enhanced load balancing
Storage Improvements
1- Generic Ephemeral Volumes are graduating to stable. This allows you to use any StorageClass as the source for an ephemeral volume, not just the default storage class.
2- Kubelet CSI Node Registration allows kubelet to register itself with a CSI driver. This is useful for CSI drivers that need to track kubelet status.
3- Cross-namespace PersistentVolumeClaim support allows you to reference a PersistentVolumeClaim from a different namespace.
Observability Improvements
Kubernetes 1.24 brings several observability enhancements:
1- Stable Prometheus metrics - All Kubernetes components now expose metrics in the stable Prometheus format.
2- Kubelet metrics improvements - More detailed metrics from the kubelet for better monitoring.
3- API server metrics enhancements - Additional metrics from the API server for improved observability.
Security Enhancements
1- Service Account improvements - Service account tokens are now time-bounded, improving security.
2- RBAC improvements - New RBAC features for more granular access control.
3- Structured authentication - More structured and auditable authentication processes.
What's the catch? Is there any reason to worry?
Yes, Kubernetes 1.24 has some important changes to be aware of:
1- Dockershim removal - If your infrastructure relies on Docker, you must switch to another OCI-compliant runtime.
2- API v1beta1 removal - If you have applications or operators using v1beta1 APIs, you must migrate them to stable v1 APIs.
3- Default service account automount - Service account tokens are no longer automatically mounted by default, requiring explicit opt-in.
4- Pod security policy removal - PSP was fully removed in Kubernetes 1.25, and you should be using Pod Security Standards instead.
Summary
Kubernetes 1.24 is a significant release with major changes affecting container runtimes and APIs. Here's a recap of the key points:
- Dockershim is removed, requiring migration to OCI-compliant runtimes
- Many v1beta1 APIs are removed, requiring migration to stable v1 APIs
- Kubelet Credential Provider is now stable and recommended
- Pod Security Standards are now the recommended way to secure pods
- Service API is graduating to stable
- Generic Ephemeral Volumes are graduating to stable
- Multiple security and observability enhancements
To summarize, Kubernetes 1.24 requires careful planning for users who rely on Dockershim or v1beta1 APIs. Plan your migration accordingly and consider engaging with your container runtime vendor if you need guidance on the migration path.
Are you planning to upgrade to Kubernetes 1.24? Have you already migrated away from Dockershim? Let us know in the comments section below!
If you are interested in Kubernetes security, do not forget to check out our Kubernetes security learning center for more insights.


