
Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

PCI DSS v4.0.1 reflects a fundamental shift in how security teams are expected to operate. It’s no longer enough to rely on periodic scans or static configuration checks. The standard now emphasizes continuous monitoring, real-time detection, and the ability to prove that controls are working at all times, not just during an audit window.
In traditional environments, infrastructure changes slowly, and periodic validation is often enough to approximate reality. In cloud and Kubernetes environments, that assumption breaks down. Workloads are short-lived, configurations drift, and identity boundaries are fluid.
As a result, many PCI controls that were historically configuration-driven now require some form of runtime validation to be meaningful.
This post focuses on how Sysdig approaches that problem from an implementation perspective, and how its runtime capabilities map to specific PCI requirements.
Bridging PCI requirement gaps with runtime reality
PCI DSS spans a wide range of controls from network segmentation and access control to logging and incident response. In cloud-native environments, these controls are distributed across infrastructure, Kubernetes, workloads, and identities.
The Sysdig Secure cloud-native application protection platform (CNAPP) focuses on the part you own in the shared responsibility model: your cloud configurations, workloads, Kubernetes clusters, and the behavior of systems processing cardholder data. It doesn’t replace things like WAFs, key management systems, or secure coding practices, but it connects the dots between configuration and runtime behavior.
That connection is what allows you to answer the questions assessors increasingly ask:
- Is segmentation actually enforced in practice?
- Are only approved workloads running in PCI scope?
- Can you prove who accessed sensitive data, and when?
- How quickly can you detect and respond to suspicious activity?
Operationalizing Sysdig for PCI
Before diving into individual requirements, it’s important to understand how teams typically operationalize Sysdig for PCI DSS compliance. The goal is to turn PCI into an ongoing operational practice, not just a point‑in‑time audit exercise.
It starts with defining scope, not as a static list, but as a dynamic, real‑time inventory. In cloud and Kubernetes environments, scope changes constantly: New workloads spin up, services scale, and configurations drift over time. With Sysdig, you can continuously identify and group PCI‑relevant resources using inventory and logical groupings called Zones. Once defined, these Zones become the foundation for applying stricter policies, detections, and reporting.
Below is an example of how you can operationalize Sysdig for PCI compliance.
Define PCI scope with inventory and Zones
Use Sysdig’s inventory to locate and tag PCI in‑scope assets, including:
- Cloud accounts regions, and VPCs/VNets
- Clusters, namespaces, and workloads
- Databases, storage, and message queues holding cardholder data

Then use Zones to group PCI in‑scope resources you identified using the real-time inventory. Examples include:
- prod-pci-aws
- prod-pci-eks-clusters
- prod-pci-k8s-namespaces
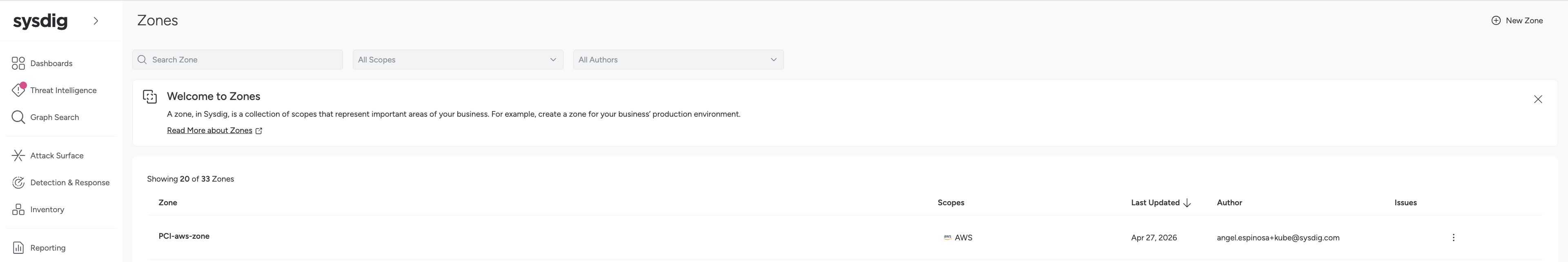
A good rule of thumb is to apply stricter policies such as PCI policies, CIS hardening, and runtime detections to PCI Zones. For non-PCI zones, you can leverage more flexible policies.
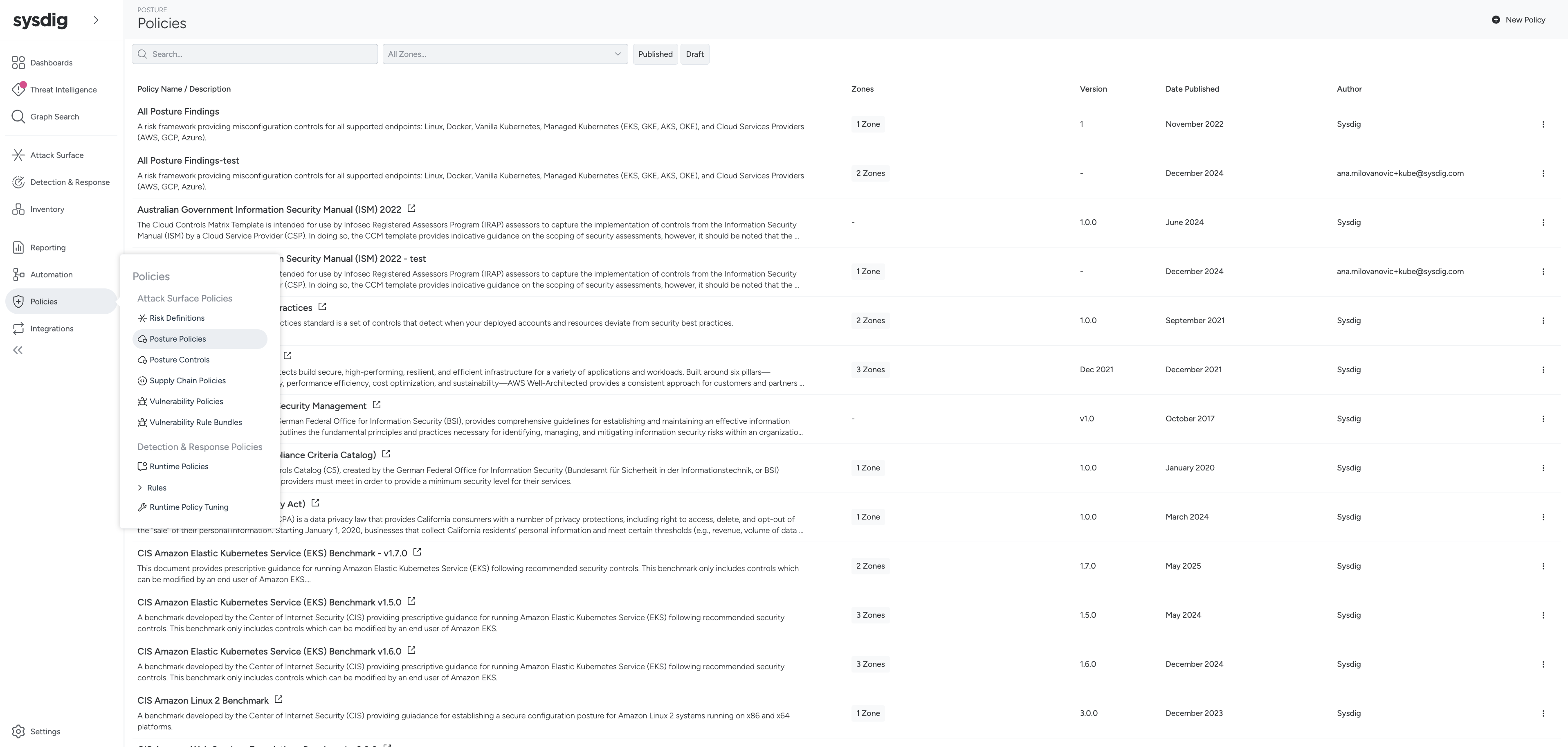
Apply PCI‑aligned policies
Sysdig offers an extensive policies library. After you’ve defined PCI scope, you can enable Sysdig’s PCI DSS policies and relevant benchmarks such CIS for cloud, Kubernetes, and OS for PCI Zones. As a best practice, map these policies to your internal PCI control matrix so that each PCI requirement contains:
- One or more Sysdig posture policies
- One or more Sysdig runtime detection sets
Next, you’ll want to focus on detections.
Configure detections and alert routing
Real-time detection is an important aspect of PCI compliance assurance. You can enable Sysdig runtime detections relevant to PCI, including:
- Network: anomalous egress, lateral movement
- Identity: privilege escalation, unusual account use
- Malware/exploit behavior: crypto miners, reverse shells
- Data access: abnormal file/process behavior on PCI hosts
Once you’ve enabled relevant runtime detections, you can route alerts into your existing workflows for SIEM, SOAR, ticketing, and on-call tools, leveraging Sysdig’s extensive cloud ecosystem integrations with leading vendors.
Evidence collection and reporting
Gathering evidence and having the data in place for audit readiness is a key component of PCI compliance. Sysdig offers compliance dashboards filtered to PCI Zones for ongoing evidence collection for posture scores, failing controls, and exceptions. You can also leverage dashboards for runtime alerts and incident timelines.

Sysdig Reporting can provide recurring PCI evidence, including mass data exports to send posture, findings, and alerts data to data warehouses like Snowflake, BigQuery, and Redshift, or governance, risk, and compliance (GRC) tools and integrated risk management (IRM) tools.
All of these capabilities within Sysdig help you transform PCI from a checkpoint compliance exercise into an ongoing operational practice to continuously monitor and enforce security posture.
Runtime security across PCI requirements
Let’s walk through how Sysdig Secure supports individual PCI requirements.

Requirement 1: Network security and segmentation
Network segmentation is traditionally validated through configuration review and occasional testing. In Kubernetes environments, service-to-service communication is dynamic, and configuration alone does not provide a complete picture.
Sysdig observes network activity with kernel-level and container-level visibility into source and destination IPs and ports, workload entities such as namespace, deployment, and pod, and network paths into and within PCI Zones. Sysdig also analyzes VPCs and VNets, subnets, route tables, and NACLs, as well as security groups and load balancers.
This visibility allows you to reconstruct communication patterns based on actual traffic. This enables two things:
- Detection of deviations from expected communication paths
- Validation of exposure based on reachability, not just configuration
The second point is particularly relevant for PCI, where scope is influenced by what systems are actually accessible.
Examples of representative runtime controls:
- Workload defined in default namespace
- Workload sharing hostNetwork
- Workload sharing hostPID / hostIPC
- Container with NET_RAW capability
Requirement 2: Secure configuration and drift control
Configuration drift is expected in cloud environments. The relevant question is how quickly it is detected and whether it can be prevented from impacting production systems.
Sysdig continuously evaluates cloud and Kubernetes configurations against policies and benchmarks. When drift occurs, it is surfaced as a finding tied to the affected resource.
More importantly, Kubernetes admission controls can be used to enforce certain policies at deployment time. This shifts some controls from detection to prevention.
At runtime, syscall telemetry provides an additional layer of validation. Even if logs are modified or incomplete, system-level activity remains observable.
Examples of representative runtime controls:
- Container running as privileged
- Container with any additional capability
- Kubelet – disabled read-only-port
- Kubelet – enabled make-iptables-util-chains
- Container with RunAsUser root or not set
Requirement 3: Protecting stored data
PCI requires not just protection of stored data, but visibility into access. Sysdig offers runtime file integrity monitoring (FIM) and process activity monitoring. This allows detection of patterns such as:
- Processes accessing files outside their expected scope
- Unusual read or write activity on sensitive paths
Because these events are tied to process and container context, they can be traced back to the originating workload and identity. This is particularly useful for forensic analysis, where reconstructing access patterns is often required.
Examples of representative runtime controls include:
- Secrets – env variable exposing secret
- Secrets – env variable exposing key from secret
- API Server – disabled basic-auth and token-auth
- API Server – defined etcd-certfile and etcd-keyfile
Requirement 4: Securing data in transit
Encryption requirements are typically validated through configuration, such as enforcing TLS.
Runtime visibility adds a different perspective. By observing network traffic, you can identify:
- Use of insecure protocols
- Unexpected plaintext communication
- Anomalous outbound connections
This does not replace configuration validation, but it helps identify cases where controls are bypassed or misapplied. By combining this with exposure analysis, teams can prioritize hardening efforts to focus first on services that are actually reachable from outside the environment.
Examples of representative runtime controls:
- ElastiCache - encrypted in transit
- API Server – disabled http
- API Server – defined secure-port
- API Server – defined tls-cert-file & tls-private-key-file
- API Server – defined client-ca-file
Requirement 5: Malware and threat detection
In containerized environments, traditional signature-based approaches are less effective due to the ephemeral nature of workloads.
Sysdig uses behavior-based detection, with Falco rules that operate on syscall patterns and process activity. Examples include:
- Reverse shells
- Cryptomining behavior
- Execution of suspicious binaries
Because detection occurs at runtime, it applies equally to short-lived and long-lived workloads.
When a threat is detected, actions such as terminating a compromised container or isolating a workload can be automated, helping contain incidents before they impact cardholder data.
Requirement 6: Vulnerability management
PCI requires organizations to identify and remediate vulnerabilities, but does not prescribe how to prioritize them.
Sysdig incorporates runtime context to prioritize vulnerability management. Specifically, it considers whether a vulnerable component is:
- Present in a running workload
- Exposed to potential attackers
- Part of PCI scope
This reduces the number of vulnerabilities that require immediate action and aligns remediation efforts with actual risk. It also integrates earlier in the lifecycle, scanning images and infrastructure as code before deployment, and enforcing policies that prevent risky artifacts from entering production.
Examples of representative runtime controls:
- No images without health checks
- API Server – defined audit-log-path and audit-policy-file
- Kubelet – disabled event-qps
- Auditing configured for /usr/bin/dockerd
Requirements 7 & 8: Identity and access controls
Identity is a critical control plane in cloud environments, and PCI places strong emphasis on least privilege and secure authentication. IAM policies define what access is allowed, but they do not provide visibility into how access is used.
Sysdig correlates identity data with runtime activity. This enables detection of:
- Privilege escalation
- Use of identities in unexpected contexts
- Access patterns that deviate from baseline behavior
From an audit perspective, mapping between identity and action is often required to demonstrate control effectiveness.
Examples of representative runtime controls:
- Create Pods (over‑broad permission)
- Over‑permissive access to “all objects”
- Over‑permissive access to resource types in a group
- Cluster‑admin members
- Only trusted users in docker group
- Compute – disabled project‑wide SSH keys
- Storage – appropriate access key rotation
- Etcd – unique Certificate Authority
Requirement 10: Logging, monitoring, and incident response
PCI DSS v4.0.1 places an emphasis on the completeness and timeliness of logging.
Sysdig captures telemetry at the system level, including process execution, network activity, and system calls. This data is independent of application logs and can be used to reconstruct events even if higher-level logs are missing.
Events are correlated across cloud, Kubernetes, and runtime domains, which simplifies investigation by providing a unified timeline.
Investigation timelines make it easier to reconstruct events, while integrations with SIEM and SOAR platforms allow teams to plug into existing workflows and automate response.
Examples of representative runtime controls:
- Logging – enabled admin‑read/data‑read/data‑write logging
- API Server – defined audit-log-path
- Logging – enabled DNS logging
Requirement 11: Continuous testing and assurance
The shift from periodic testing to continuous validation is largely addressed through the combination of posture and runtime signals.
Configuration checks validate the intended state. Runtime detections validate actual behavior. Together, they provide a continuous signal on whether controls are functioning as expected.
Requirement 12: Evidence and audit readiness
Evidence generation is often one of the more operationally expensive aspects of PCI. Because Sysdig continuously collects both posture and runtime data, much of the required evidence for an activity audit already exists as a byproduct of normal operation.
Dashboards and reports can be filtered to PCI scope, and historical data can be exported as needed. The key difference is that evidence reflects both configuration and observed behavior, rather than relying solely on point-in-time snapshots.
Conclusion
PCI DSS v4.0.1 is ultimately about continuous assurance. It requires organizations to move beyond static checks and demonstrate that security controls are effective in real-world conditions.
Sysdig helps you get there by:
- Reducing your attack surface across cloud and Kubernetes environments
- Detecting and responding to threats at runtime
- Continuously validating controls through posture and behavior
- Providing audit-ready evidence without last-minute effort
When combined with your existing controls like network segmentation, secure application design, and key management, Sysdig becomes a central pillar of a runtime-driven PCI strategy.
To see how Sysdig can help you enhance your PCI compliance, book a demo today.

.jpg)
