Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

Security teams today have more data than ever before. Modern cloud security tools surface vulnerabilities, misconfigurations, and other alerts at massive scale, giving organizations widespread visibility into their environments and where risk is present. Over the past several years, security programs have also made real progress on prioritization, helping narrow that data down to the issues that matter most.
But identifying risk is only the first step. Security teams are ultimately measured by how effectively they reduce risk, not by how much of it they can see.
A prioritized vulnerability that is not fixed is still a vulnerability that exposes the environment. Even well-understood risks can cause issues when there isn’t a clear path to address them. The real challenge organizations face is consistently translating the large volumes of data their tooling produces into the right actions at the right time.
The gap between data and action
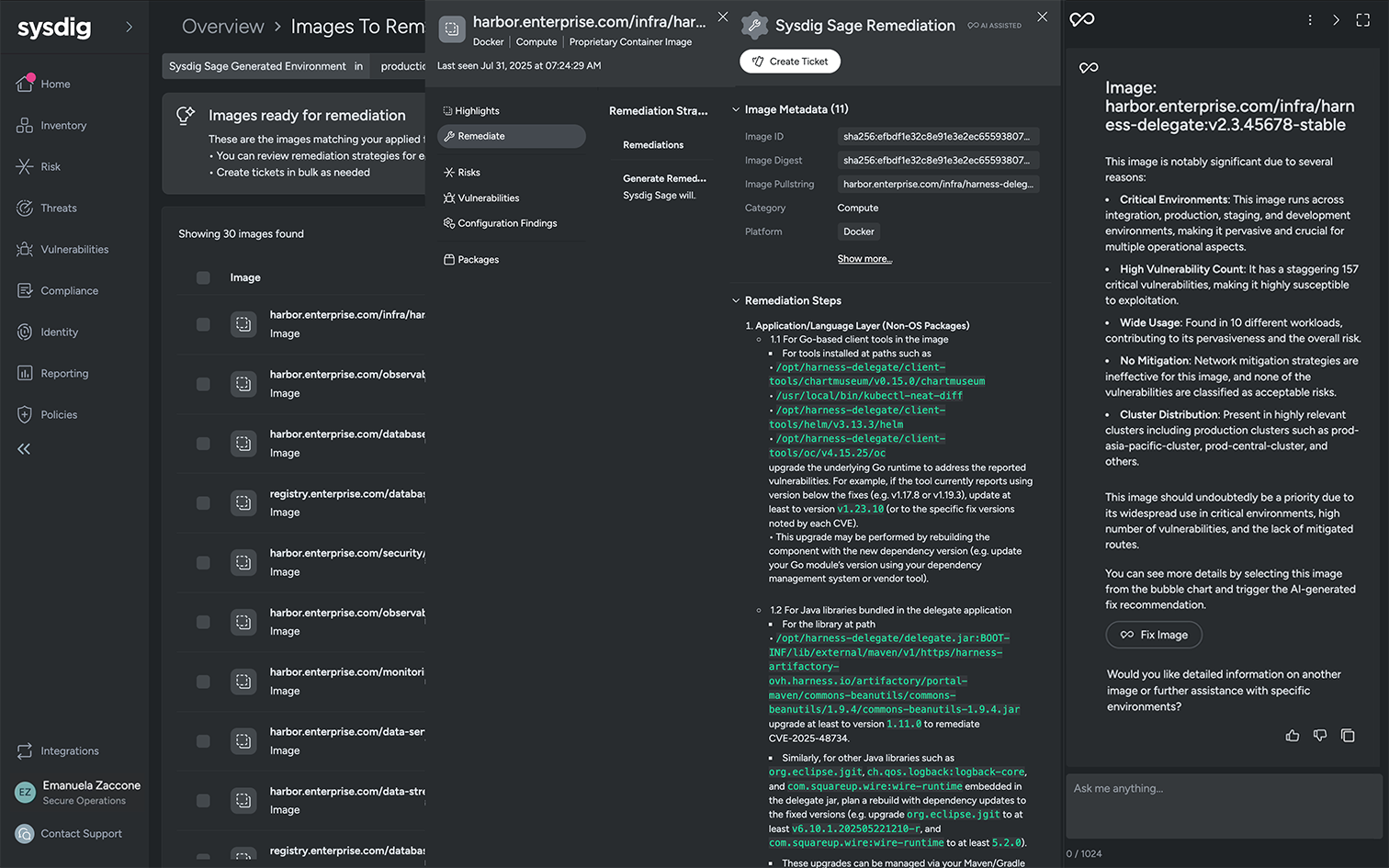
For many organizations, this gap between insights and response shows up in everyday security workflows. One common use case where this appears is vulnerability management. In a typical scenario, security teams scan their environments and prioritize thousands of vulnerabilities, narrowing them down to a smaller set of high-risk issues. This is an important part of the process, but those vulnerabilities still need to be fixed, and in many cases, they can stay unresolved for weeks or longer.
At the core, this problem often comes down to context. Security often has to rely on other teams to patch vulnerabilities, like development teams who own the specific image or package. Acting on these findings requires full context of why the vulnerability is important and practical guidance on how to fix it. Without this level of clarity, developers who own vulnerabilities can feel like these requests are distractions from core development work, and even issues at the top of the priority list can stall, leaving known risk unresolved.
The same pattern appears in threat detection. Alerts can surface suspicious behavior, but they do not resolve the incident. Teams still need to understand what happened, determine the blast radius, and take action to stop it. Until that happens, the threat remains active, and the environment remains exposed.
What taking action looks like today
The key moment in modern cloud security is what happens next after the risk is identified. In the scenarios above, this means actually remediating vulnerabilities before they are exploited and responding to threats in real time as they occur.
Effective vulnerability remediation requires context
On the vulnerability management side, effective action is about fixing the vulnerabilities that meaningfully reduce risk, not just fixing everything. Updating everything to the latest version may eliminate vulnerabilities on paper, but it can also create instability across the application. Developers aren’t going to risk breaking critical systems just to clear a list of CVEs.
Taking action means identifying the fixes that address the most risk without breaking application dependencies, applying them efficiently, and resolving issues at the source so they do not repeatedly surface in future builds.
Once these fixes are identified, they need to be automatically routed to the proper owners with context on their impact. For example, a single patch may address vulnerabilities across multiple workloads. They also need clear, actionable remediation guidance on which patches to apply. AI is increasingly helping to bridge this gap by analyzing vulnerability data and translating it into practical, easy-to-follow remediation steps. With this level of clarity, remediation becomes more focused and more efficient, reducing both risk and wasted effort.
Effective remediation requires real-time insight
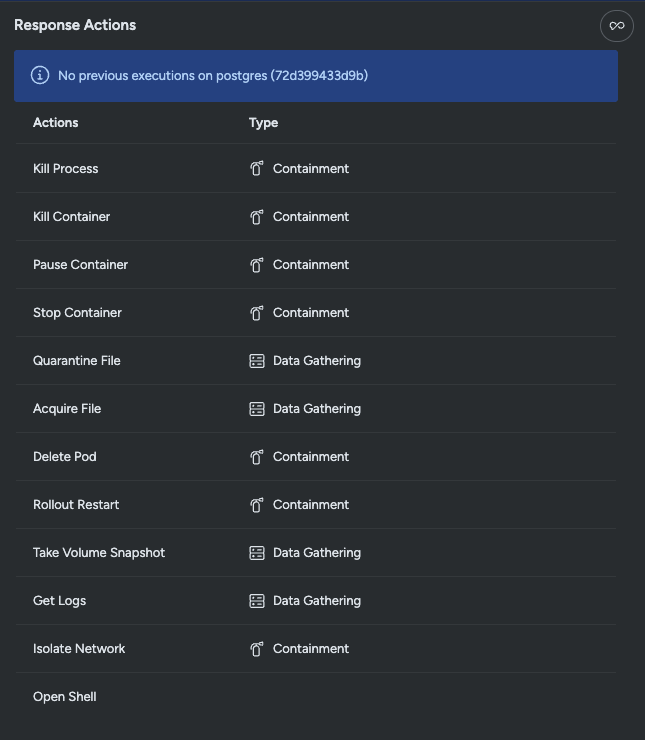
On the threat detection side, action begins once suspicious behavior is detected. SecOps and SOC teams need to move quickly from detection to understanding to containment. This involves determining what triggered the alert, what systems are affected, and whether the activity represents a real threat. This requires rapid investigation, correlating related events across systems to build a clear picture of what actually happened before taking action.
From there, action becomes more concrete. Teams may isolate a suspicious network connection to prevent further communication, stop the container where the malicious process was running, or restart a compromised workload to remove persistence. At the same time, they may collect logs or forensic data to better understand what occurred and prevent similar issues in the future.
What matters in both these scenarios is speed and precision. Overly broad or delayed response actions can be disruptive or incur downtime costs if systems are taken offline. Effective action targets the specific issue, limits impact, and reduces risk without unnecessary side effects.
How security teams deliver value
Visibility and prioritization remain essential steps of cloud security, but they don’t reduce risk on their own. Vulnerabilities that remain open and threats that remain active continue to expose the business, regardless of how well they are understood.
Security outcomes are defined by what gets fixed, contained, and resolved before real damage can be done. Taking action is where security proves its value, delivering outcomes that the business can clearly see and measure.