Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

Why fragmented cloud security workflows create risk and slow response
The current state of cloud security for many organizations is a lot like the Ford Mustang I had as a teenager: Fast, noisy, and somehow functioning with a series of aftermarket parts slapped together.
Each modification solved a specific problem or increased horsepower, but none of them were designed to work with the others as a cohesive system. The suspension wasn't ideal, the brakes were inadequate, and traction was limited. In hindsight, that was kinda scary.
That’s how many security workflows operate today. Alerts, notifications, ticketing, and response actions all exist, but they’re often spread across separate tools, workflows, and manual processes. This can “work,” but it’s inefficient, inconsistent, and hard to scale.
As cloud environments grow more complex, this fragmented approach slows teams down when it matters most.
How Sysdig Automations connect detection, investigation, and response
Sysdig Automations is the shift from that patched-together Mustang to something engineered to perform as a complete system, like a Formula 1 Ferrari where every component works in sync.
Instead of stitching together alerts, notifications, tickets, and response actions across disconnected tools and manual processes, Automations gives teams a single place within the platform to design logic flows from trigger to outcome.
Starting from events like new risks, threats, vulnerabilities, or runtime events, users can build workflows with branching conditions that route notifications, create tickets, or execute response actions such as investigation or containment steps.
For DevSecOps and SecOps engineers, this means less manual effort, less noise, and more consistent workflows. For security leaders, it can reduce the need for separate orchestration platforms by bringing everything together into one cohesive system.
Cloud security automation use cases: Risks, vulnerabilities, threats, and runtime events
Sysdig Automations isn’t about building abstract workflows (even though you can do that). It’s about handling the moments that normally slow teams down by eliminating manual and repetitive busywork.
Take risk updates. When a new risk appears or expands to impact additional resources, teams typically have to figure out who owns what and where it should go. Automations handles that upfront. The same risk can be routed differently depending on whether it touches an S3 bucket, an EC2 instance, or an IAM role, so Automations ensures that the right team gets notified without someone manually triaging every update.
Vulnerabilities are another area where this matters. Instead of treating every finding the same, analysts can focus on the ones that actually carry risk, like critical vulnerabilities with known exploits in a specific zone. Automations lets you prioritize those signals and route them into existing workflows like Slack, PagerDuty, or Jira, with enough context included to take action quickly instead of chasing down details.
Accepted risk is where things often fall through the cracks. Exceptions get created, then forgotten. With Automations, those decisions stay visible. Notifications can be triggered when a risk is about to expire or when something changes, so temporary exceptions don’t quietly turn into long-term exposure.
At runtime, the value becomes even more immediate. When a high-severity event fires, the question is always “who handles this, and what happens next?” Automations connects that detection directly to action. The right team is notified, additional context can be pulled in, and response steps can be triggered without breaking the investigation flow.
The same idea applies to threats. Instead of treating every detection as a one-off, efficient teams can now define how different types of threats should be handled based on where they occur and what they impact. That removes a lot of repetitive triage and makes response more consistent across environments.
And behind all of this, executions provide a clear record of what actually happened. Every time an automation runs, you can see the exact path it took, what conditions were evaluated, and which actions succeeded or failed. That visibility makes it easier to trust the workflows you’ve built and adjust them when needed.
How Sysdig Automations works: Triggers, conditions, and response actions
Sysdig Automations are built directly into the Secure platform, allowing teams to create workflows that trigger from events such as new risks, threats, vulnerabilities, or runtime detections.
From the Secure UI, analysts can define logic flows using filters and preconfigured actions, tailoring workflows to match their operational needs. Each automation starts with a trigger and can branch through conditions to chain multiple actions together, such as sending notifications, creating Jira tickets, or initiating response steps.
These workflows are configurable, allowing teams to standardize processes while adapting to different use cases across risk management, vulnerability handling, and runtime threat response.
Real-world cloud security automation use cases
Threat detection for critical resources
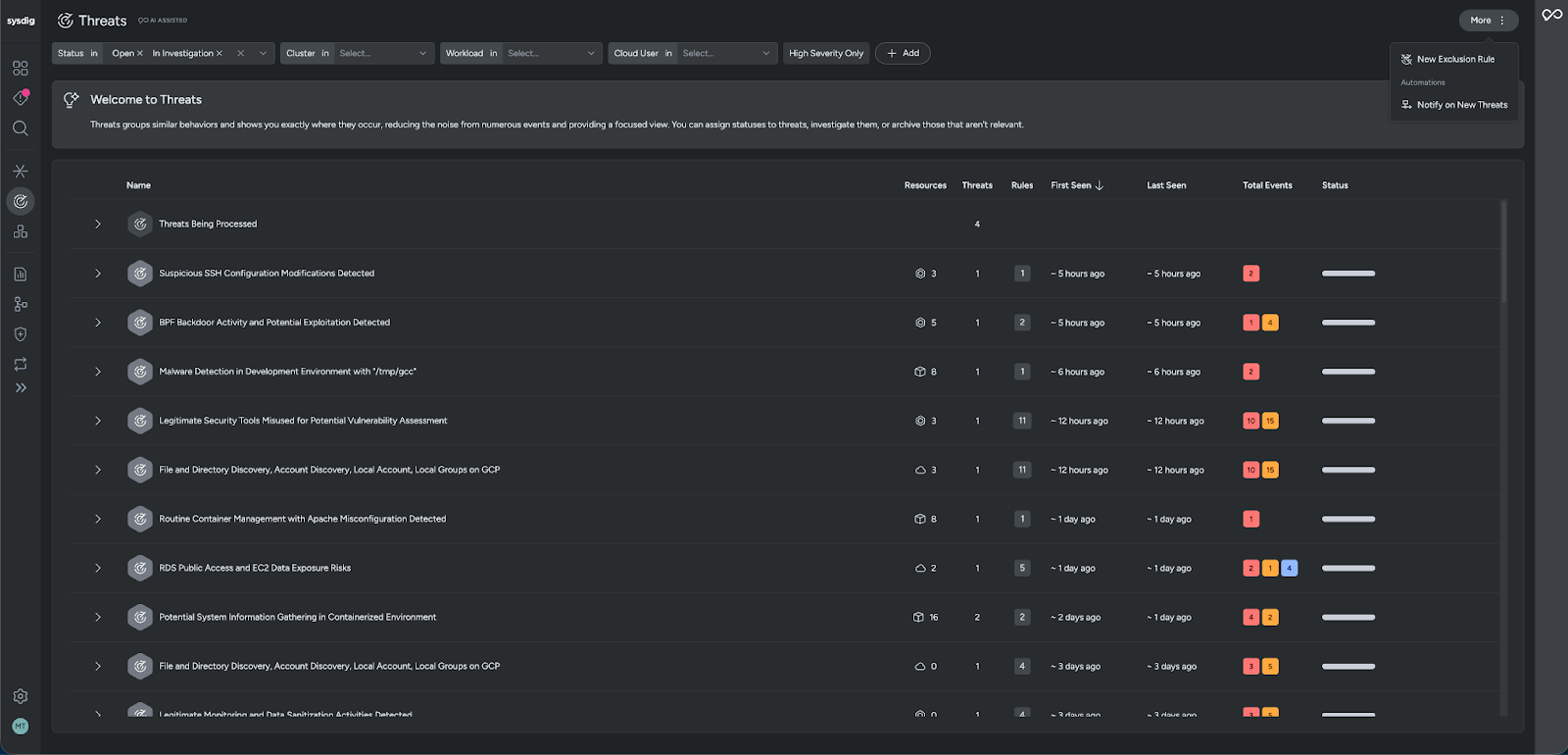
In the Threats module, we start with a view of all threats across the environment, grouped and prioritized so teams have a single place to understand what’s happening. From there, if we only care about specific parts of our infrastructure, we can filter down by what matters most; for example, narrowing to a particular cluster, a key workload, or a specific cloud user, and even focusing on high‑severity threats only so we’re not distracted by low‑risk noise.
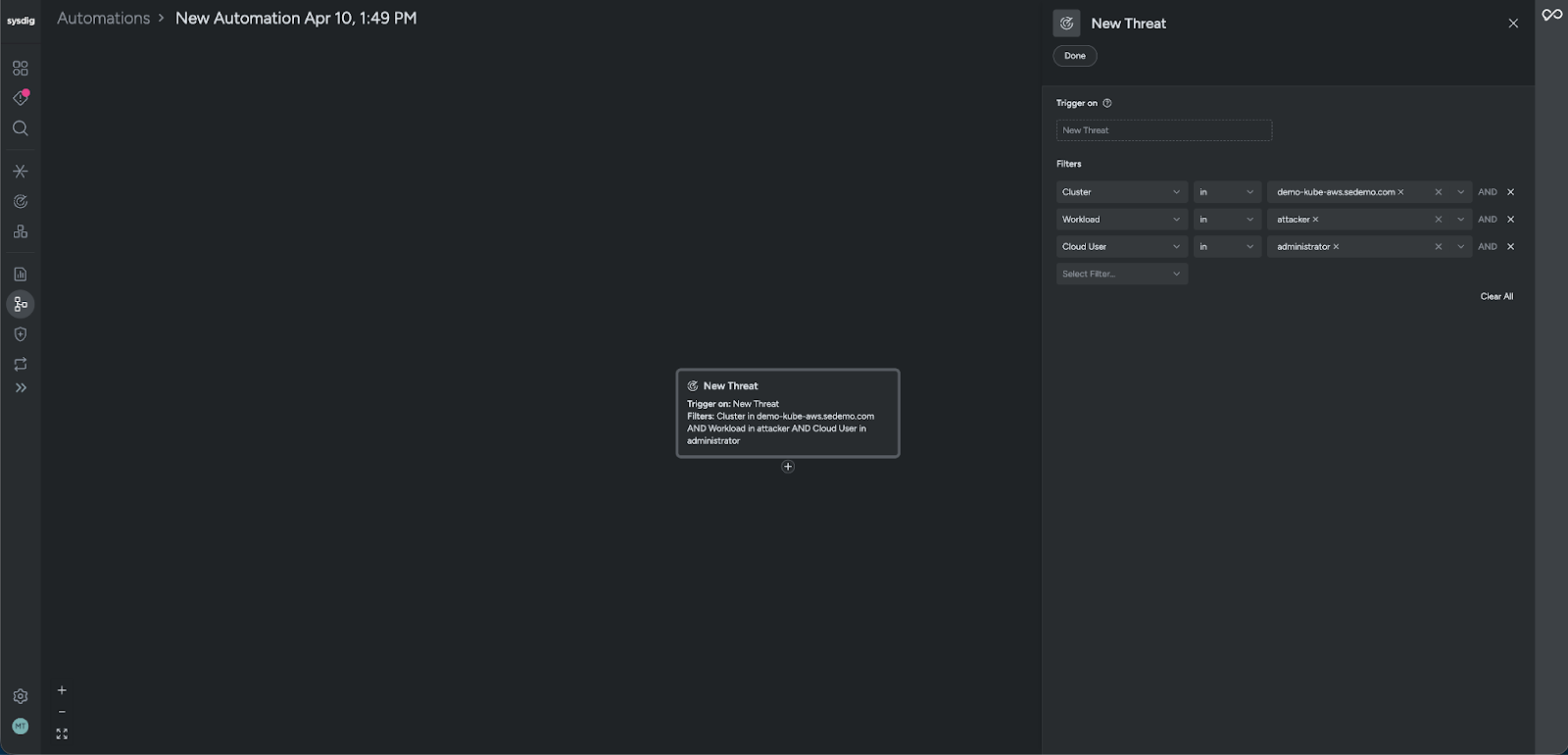
Once we’ve dialed in that view of “threats that matter” for our environment, we use Threats Automations to carry those same filters over into a workflow. Instead of constantly re-creating the view or manually watching the page, we configure an automation that listens for new threats matching those filters.
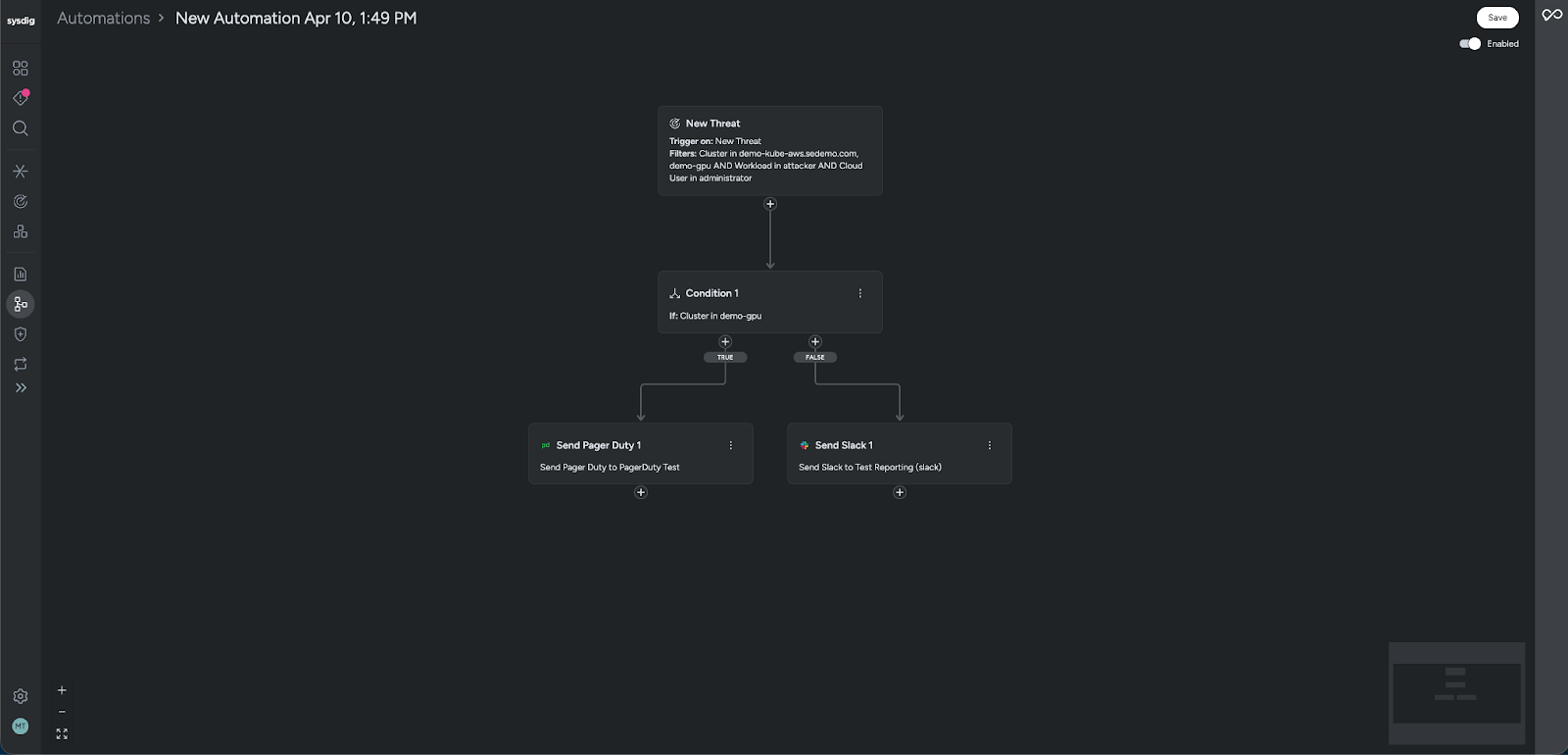
When a new matching threat appears, the automation automatically sends notifications via Slack, Microsoft Teams, Email, Webhook, PagerDuty, or SNS, so the right team is alerted in their existing tools without having to camp in the UI.
This flow turns a filtered, contextual Threats view into a living alerting pipeline that tracks just the high‑priority parts of the estate and pushes updates directly into the channels teams already use.
Vulnerability management with Jira integration
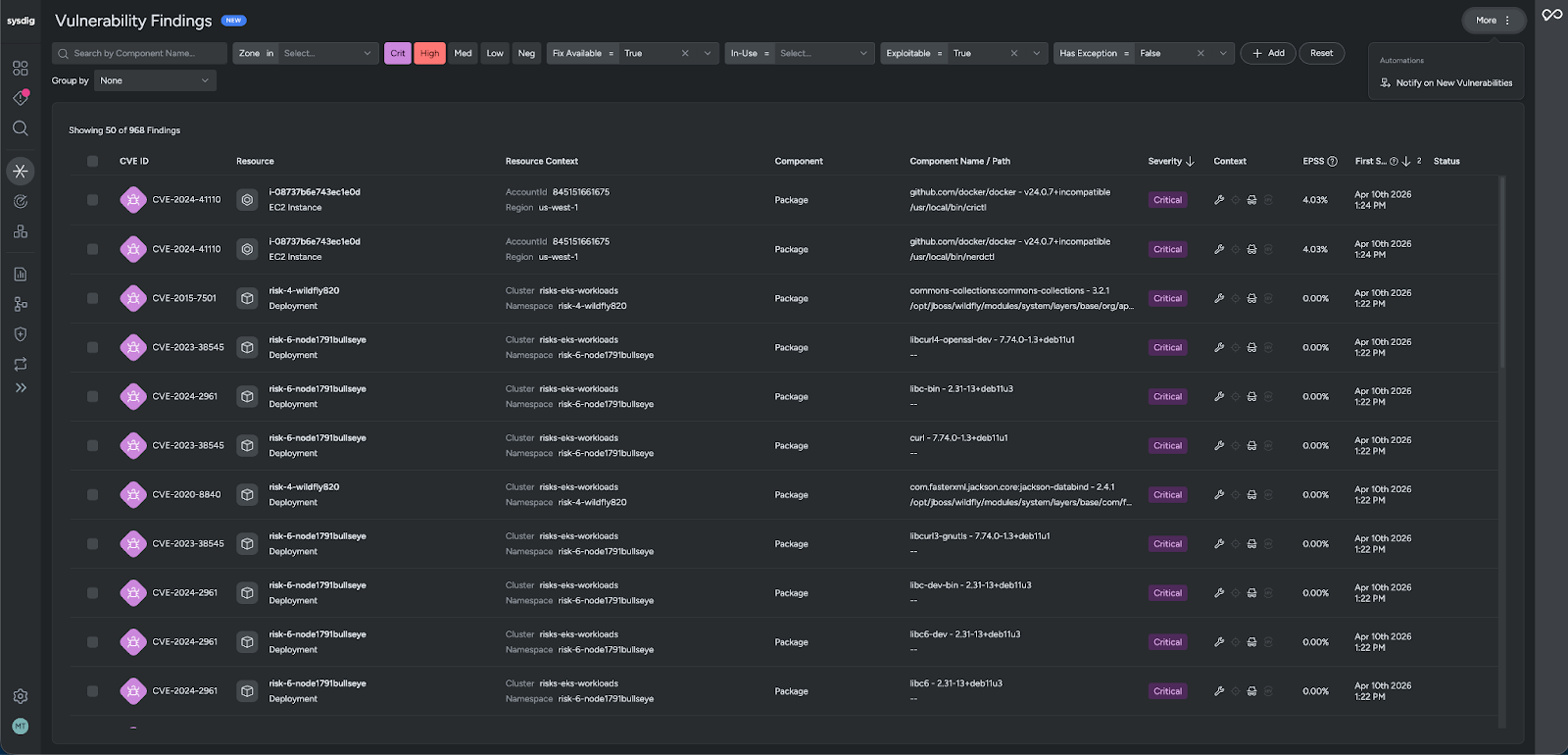
For vulnerability management, we begin on the Vulnerability Management Findings page, where we see all image and host vulnerability findings across our resources. To focus on what really matters, we first filter down to important resources or Zones — for example, production clusters, critical business applications, or specific Zones. We then tighten this further by filtering only to Critical findings or those that are In‑Use and Exploitable, and we can even group by resource so we see issues in the context of each image, workload, or host.
With that curated view in place, we use Vulnerability Findings Automations to notify on new vulnerabilities that match these filters. The automation reuses the same criteria (zones, severity, exploitability, resource grouping), so any new high‑risk finding on those important resources automatically triggers a workflow.
From Automations, we have two main paths:
- Stay at the notification layer: Send updates to Slack or Email, so security and owning teams are kept in the loop when new exploitable issues appear in their area.
- Go deeper into the developer workflow: Automatically create Jira tickets using the configured Jira integrations. When the automation runs, it can select the appropriate issue type (Task, Epic, or Bug) from the configured options and open a ticket with the right project, labels, and vulnerability details populated.
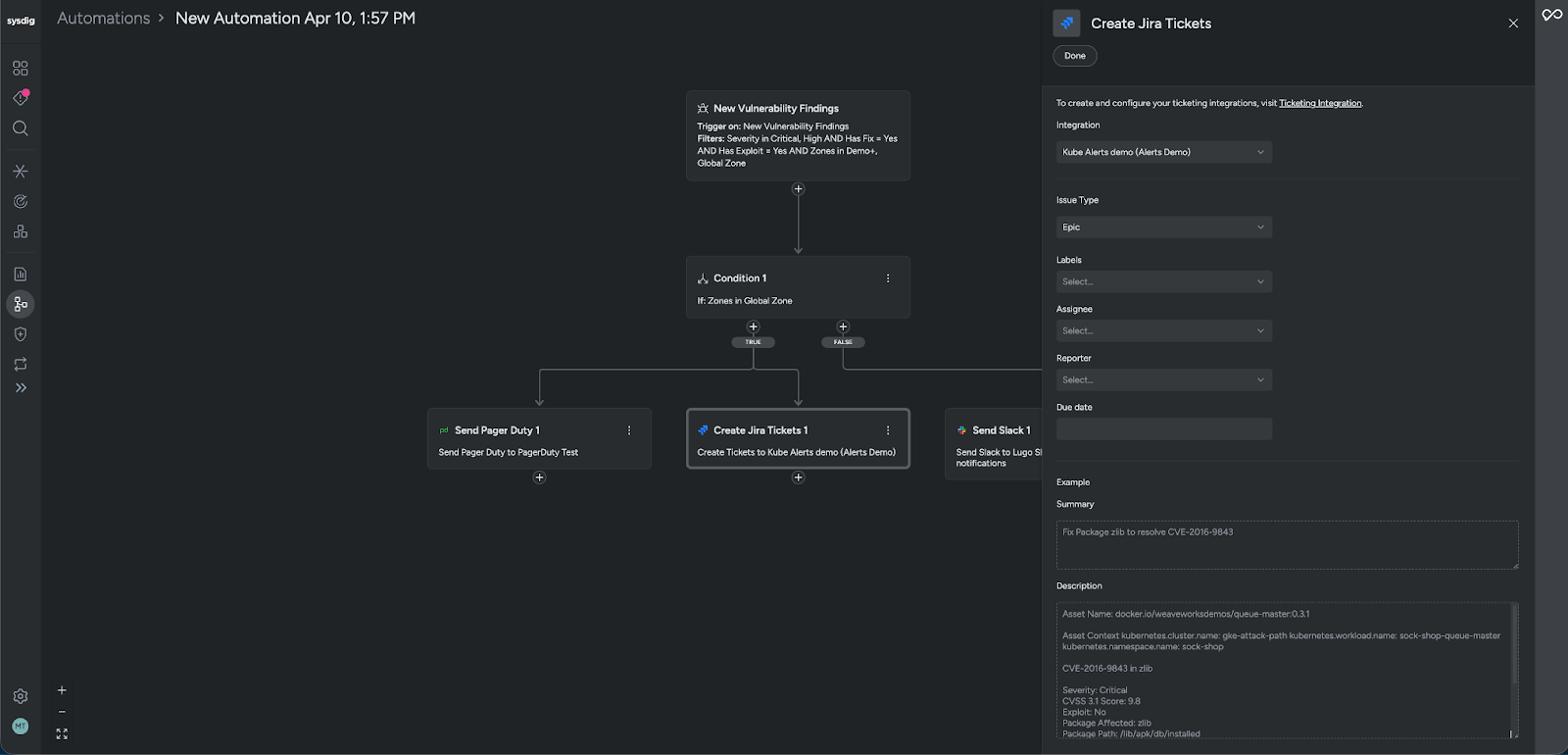
This turns the VM Findings view into a continuous handoff into Jira, ensuring that critical, exploitable vulnerabilities on important resources are not only detected and surfaced, but also immediately translated into actionable work in the tools engineering teams already live in.
Benefits for DevSecOps and SecOps teams: Faster, more consistent response
For DevSecOps and SecOps practitioners, Sysdig Automations reduces repetitive manual steps that slow teams down. Instead of repeating the same manual steps for every alert, common tasks can be automated, standardizing how workflows are executed and ensuring responses are consistent across environments.
By bringing detection, notification, ticketing, and response into a single system, practitioners can stay within one platform and avoid constant context switching between tools.
In addition, all automations are fully auditable, giving teams clear visibility into what actions were taken, when they occurred, and how workflows executed, supporting transparency and governance.
The result is a more streamlined workflow where security teams can do it all in one place, reducing operational overhead while improving the speed and reliability of their response.
Benefits for security leaders: Tool consolidation and improved ROI
For security leaders and platform owners, Sysdig Automations delivers value by reducing reliance on external workflow and orchestration tools.
By consolidating detection, notification, ticketing, and response into a single platform, organizations can simplify their tooling landscape and reduce the operational overhead that comes with maintaining multiple integrations and systems.
This consolidation improves the efficiency of security teams by enabling faster, more consistent workflows while maximizing the value of the existing Sysdig platform. Ultimately, this helps drive better ROI by turning Sysdig into not just a detection tool, but a unified system for coordinated response.
Why cloud security teams need workflow automation now
As cloud environments scale and become more dynamic, the fragmented workflows many teams rely on today introduce operational risk.
Security processes spread across alerts, notifications, ticketing systems, and response tools may function, but they are often inefficient, inconsistent, and difficult to scale under pressure. This disjointed approach slows response times at the exact moment speed matters most, increasing exposure as threats unfold in real time.
Sysdig Automations addresses this by bringing these disconnected pieces into a single, cohesive system, enabling teams to move from detection to action with greater consistency, efficiency, and control as cloud complexity continues to grow.
From alerts to action: Automating cloud security response with Sysdig
Fragmented workflows might get you moving, but they won’t win you the race. As cloud environments demand faster, more coordinated response, stitching tools together is no longer enough.
Sysdig Automations replaces that patchwork with a system designed to work as one, so teams can move with precision, act without delay, and turn detection into decisive action when it matters most.
Schedule a demo to see how it works in your environment.


