
Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

Why forensics breaks down in the cloud
When a security incident occurs, alerts provide critical context, but they are only the starting point for understanding what actually happened. Security teams still need to determine how an activity began, how it progressed, and what was ultimately impacted.
In traditional environments, that process was more forgiving. Systems were long-lived, and evidence persisted long enough to investigate after the fact. Teams could rely on logs and system state to reconstruct events with reasonable confidence.
That model does not hold in cloud-native environments. Containers are ephemeral, workloads are constantly changing, and infrastructure is abstracted away. If the relevant activity is not captured while it is happening, it may no longer exist by the time an investigation begins. When that happens, even well-instrumented detections can leave gaps in the full sequence of events.
This is where many teams run into challenges. Detection is fast and increasingly rich in context, but fully reconstructing what happened at the system level can still take time, especially in dynamic environments.
Extending detection with runtime forensics
Effective cloud forensics requires visibility into what is happening while workloads are running, not just after they are gone. Sysdig Secure delivers this by combining detection, context, response, and forensic visibility into a single platform.
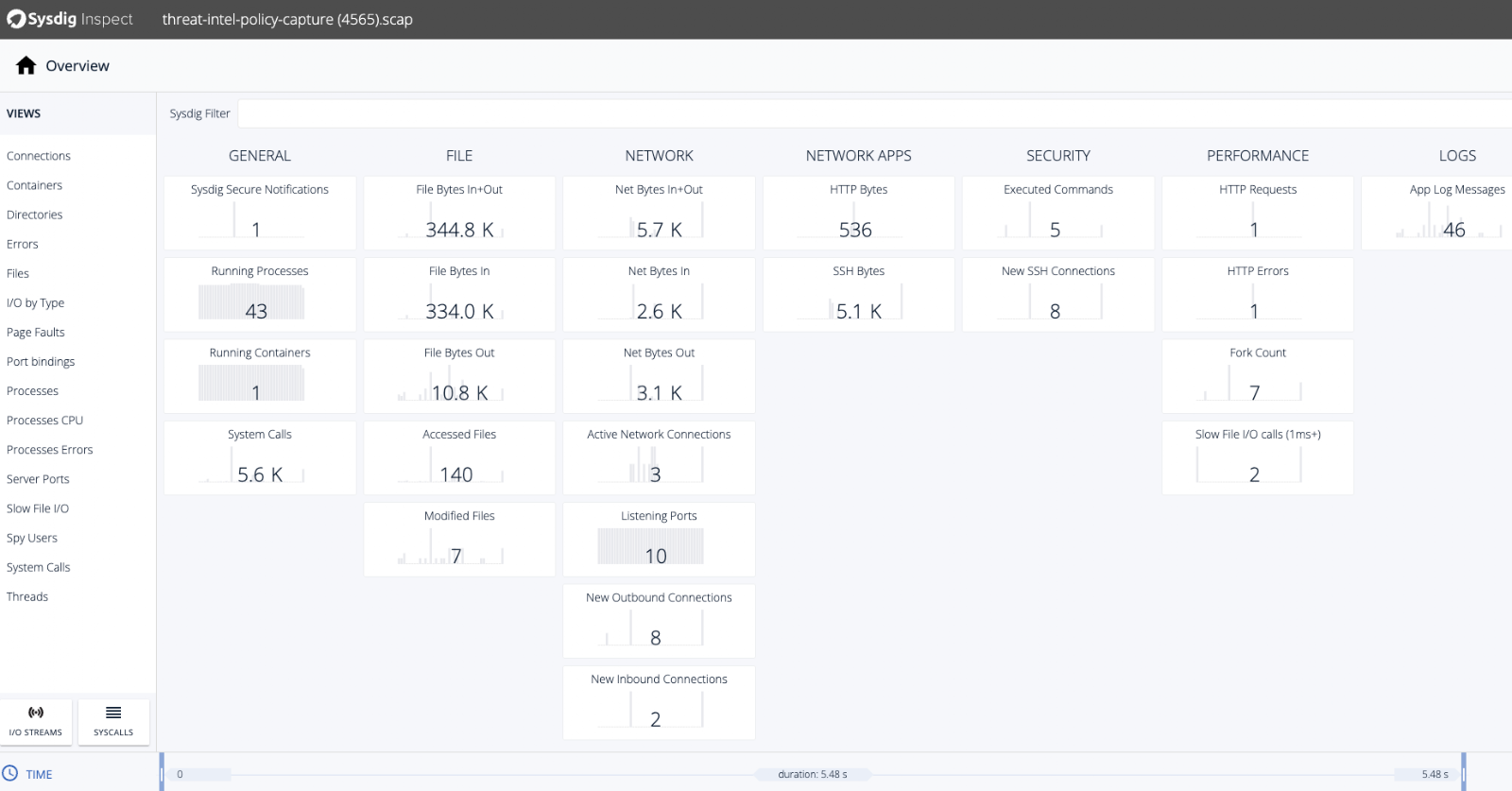
Sysdig Inspect is a feature within Sysdig Secure that enables deeper forensic analysis of runtime activity. Sysdig captures system-level activity during execution, and Inspect allows analysts to explore that data directly within the same interface.
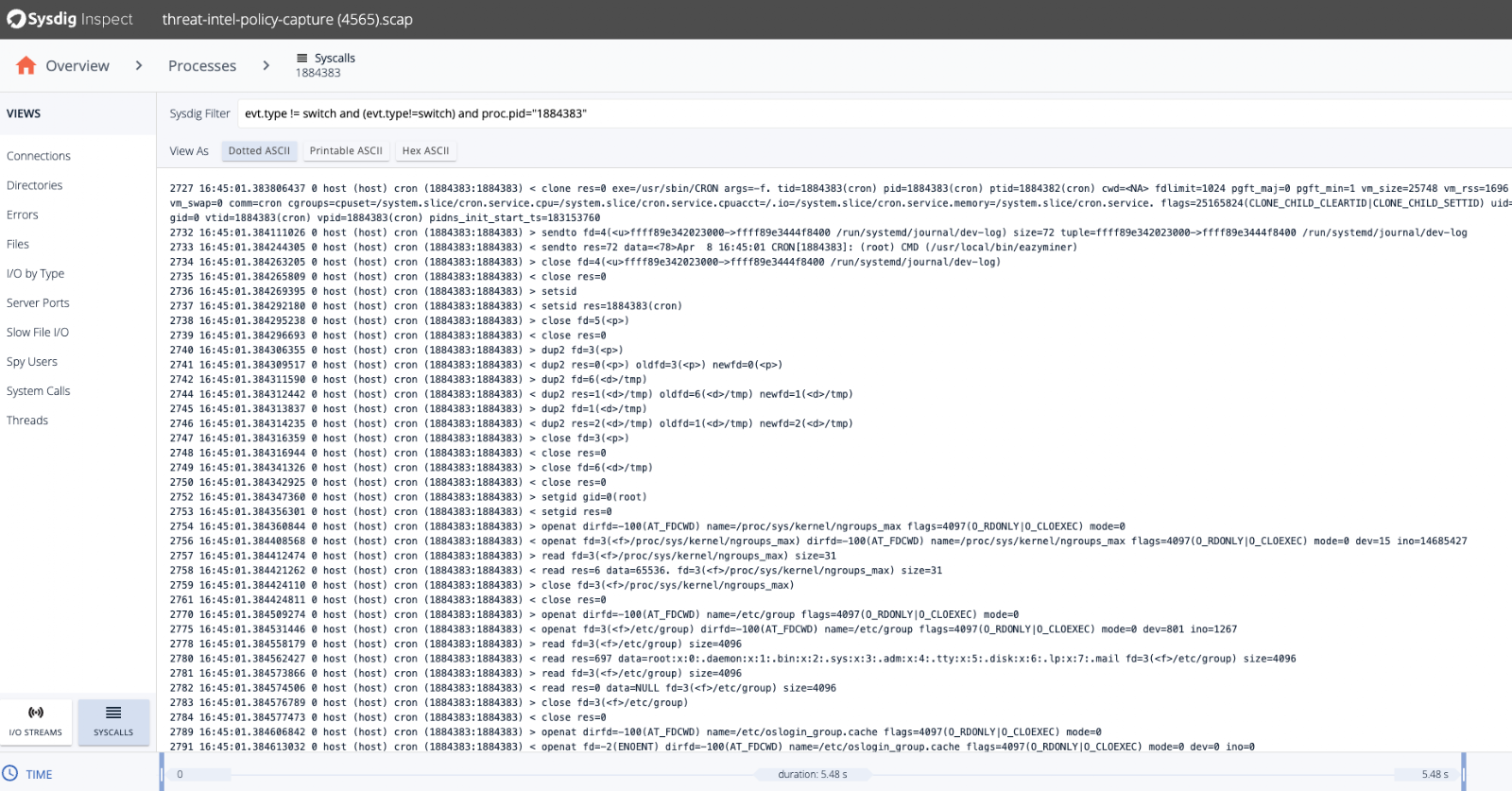
Instead of continuously collecting and sifting through overwhelming volumes of data, Sysdig Inspect and captures allow teams to zoom in at the moment a specific detection occurs. Analysts can then drill into different data types in isolation, examining processes, connections, and files before going deeper into system calls. This structured approach reduces noise, eliminates the need to sift through unrelated activity, and ensures investigations stay focused. The result is visibility that is both precise and actionable.
All this builds on the context already available in Sysdig Secure. Alerts provide the context to understand why a detection occurred, and Sysdig Inspect provides the evidence within the same platform to validate exactly how it happened.
Reconstructing the full sequence of events
One of the most time-intensive parts of incident response is turning an alert into a clear, defensible timeline.
Alerts in Sysdig Secure provide rich context around detections, including the triggering behavior, affected resources, and associated activity. But in complex scenarios, investigators often need to go deeper to understand how the activity originated and how it evolved over time.
Since Sysdig Inspect is built directly into Sysdig Secure, analysts can reconstruct that sequence using captured runtime data without leaving the investigation workflow. Because captures are scoped to the investigation, teams benefit from data collected only when needed, rather than managing constant high-volume telemetry.
Analysts can follow process execution, examine parent-child relationships, and trace activity step by step, with full visibility into process lineage, file access, network activity, and system-level behavior.
With Sysdig Inspect and captures, instead of continuously collecting and sifting through overwhelming volumes of data, teams can zoom in at the moment a specific detection occurs without being flooded with constant noise or having to sort through unrelated activity to find what matters. This approach ensures visibility is both precise and actionable.
In this way, Sysdig allows teams to move beyond high-level context and work directly from recorded evidence when needed.
Forensics across modern cloud environments
Cloud environments are not only dynamic; they are distributed. A single application may span containers, Kubernetes clusters, virtual machines, and multiple cloud workloads.
Sysdig Secure provides consistent detection and context across these layers, and Sysdig Inspect extends that visibility with deeper runtime analysis, all within the same platform.
Whether an event originates in a container or on a host, teams can follow the same investigative approach and maintain continuity as they analyze evidence. This becomes especially important when incidents cross boundaries, such as when workload behavior intersects with identity activity or cloud API usage.
Because forensic analysis happens within Sysdig Secure, teams can move from alert to investigation without losing context or switching tools.
Faster understanding, more confident decisions
During an active incident, time directly impacts risk.
Delays often occur when teams need to gather additional evidence, validate assumptions, or correlate data across systems. Even with strong detection context, understanding the full scope of an incident can take longer than expected.
With Sysdig Inspect embedded in Sysdig Secure, captured runtime activity is immediately accessible as part of the investigation workflow. Analysts can determine whether behavior is malicious, identify root cause, and understand impact without waiting on additional data collection or switching tools.
This leads to more confident decisions. Teams can validate what they are seeing and respond based on evidence, rather than relying on assumptions or incomplete information.
Built for real-world investigations
Investigations are rarely linear. Analysts follow leads, test hypotheses, and adjust direction as new information emerges.
Sysdig Secure supports this workflow by centralizing detection, investigation, and response. Sysdig Inspect enhances that experience by allowing analysts to explore detailed runtime activity within the same interface.
Investigators can move from summarized alert context to granular forensic evidence, follow relationships between events, and build an understanding in real time. This reduces manual correlation and eliminates unnecessary context switching during critical moments.
Forensics that keeps pace with the cloud
Cloud-native environments move quickly, and threats move just as fast. Detection alone is not enough. Teams need to understand activity quickly enough to take effective action.
With Sysdig Inspect as part of Sysdig Secure, teams can access captured runtime activity to investigate incidents in depth without leaving the platform. This makes it possible to establish a sequence of events, identify root cause, and validate findings using system-level evidence, even in fast-moving, ephemeral environments.
In the cloud, the real challenge is not just detecting that something happened.
It’s understanding exactly how it happened before the opportunity to act is gone.
Schedule a demo today to see how Sysdig Inspect, built into Sysdig Secure, enables cloud-native forensics in your environment.


