Browse all content by asset type.
Introducing the Sysdig open source community
DEFENSE REPORT
AI Helps Teams Reduce MTTR by 76%
Sysdig named representative vendor in Gartner Market Guide for CNAPP
Blog Posts

Malicious NPM packages: Are you exposed?

How runtime insights power every cloud security use case

AI for SOC teams: 5 cloud security prompts to start your day with Sysdig Sage™
Briefs

Sysdig Corporate Brief
Founded by the creators of open source standards — Falco, Stratoshark, and Wireshark — and built on agentic AI, Sysdig delivers real-time cloud defense grounded in the uncompromising truth of runtime.
BRIEF. 2025 Cloud‐Native Security and Usage Report
This is a special edition of Sysdig’s 2025 Cloud-Native Security and Usage Report, providing only the usage and analysis of the open source detection tool, Falco.
BRIEF. Top 5 Best Practices For Image Scanning
How do you manage container security risk without slowing down application delivery?
Case Studies

BigCommerce Achieves Real-Time Cloud Security
With Sysdig Secure, organizations were able to quickly scan their containers for impacted images and discern their risk in less than five minutes.

Retail tech company triples threat remediation speed with zero downtime and 680% ROI
A leading returns platform stopped a stealth cloud attack during peak season without downtime. See how they regained visibility, contained the threat in minutes, and turned a breach attempt into a catalyst for stronger, automated defenses.

BigCommerce Achieves Real-Time Cloud Security
With Sysdig Secure, organizations were able to quickly scan their containers for impacted images and discern their risk in less than five minutes.
Ebooks
Top 6 Use Cases for Monitoring Cloud-Native Workloads with Sysdig Monitor
Securing the Cloud: The Benefits of Falco with an Enterprise Experience
An ebook with 3 mini case studies heavily featuring Falco and how it works with Sysdig, plus a callout to Falco Feeds at the end.
Guides
Cloud Security for Google Cloud
This guide outlines key requirements and capabilities for establishing comprehensive security for Google Cloud services and containers.
Cloud Security for Amazon Web Services
This guide outlines key requirements and capabilities for establishing comprehensive security for AWS cloud services and containers.
Secure Your Cloud in Minutes - Your Checklist for Meeting the 555 Benchmark
Sysdig’s 555 Benchmark for Cloud Detection and Response offers a standard to use when measuring how fast your security teams can counter attackers. Specifically, the benchmark finds that to outpace attacks, your security teams need to detect threats within 5 seconds, correlate and triage data within the first 5 minutes, and initiate a tactical response within the next 5 minutes.Sysdig’s 555 Benchmark for Cloud Detection and Response offers a standard to use when measuring how fast your security teams can counter attackers. Specifically, the benchmark finds that to outpace attacks, your security teams need to detect threats within 5 seconds, correlate and triage data within the first 5 minutes, and initiate a tactical response within the next 5 minutes.
Infographics


2021 Container Security and Usage Snapshot
In 2020, we saw an acceleration of cloud adoption that led to an increase in container usage. This increase, combined with the fact that half of containers live less than five minutes, reinforces the need to manage container-specific security risks. Our goal is to shed light on the current state of container infrastructure, applications, security, and compliance practices.


Close the Security and Visibility Gap for Containers on AWS
Close the Security and Visibility Gap for Containers on AWS. With Sysdig you can confidently run cloud apps in production on AWS container services like Amazon EKS, Amazon ECS, and AWS Fargate. Click to learn more.


2020 Container Security Snapshot
Vulnerabilities and risky configurations inside container images highlight the need for secure DevOps. Containers and Kubernetes are being used heavily by DevOps teams deploying cloud applications. But it’s important to know what’s inside containers to manage risk effectively. Click to learn more.
Podcasts

Red Hat X Podcast
"As cloud native becomes the standard for application deployment, IT roles must adapt. Cloud teams are taking ownership for security, as well as application performance and availability. As a result they need tools and processes that support a secure DevOps workflow for Kubernetes and containers in production."
Press Releases

Cloud Security Leader Sysdig Appoints William Welch CEO to Accelerate Growth and Global Footprint
Cybersecurity veteran joins from Talkdesk, previously at Duo Security, Zscaler, and SymantecRALEIGH – Nov. 21, 2024 – Sysdig, the leader…
Falco Feeds by Sysdig Empowers Companies to Harness Open Source Security at Enterprise Scale
With detections backed by the elite Sysdig Threat Research Team, Falco Feeds equips organizations to easily scale Falco and stay…

Sysdig Annual Threat Report Highlights Growing Cost and Scale of Cloud Attacks
With a new focus on stealing cloud credentials and exploiting enterprise AI to the tune of $100,000+ per day, the…
Reports

Sysdig 2024 Cloud-Native Security and Usage Report

Cloud Detection and Response: Market Growth as an Enterprise Requirement - July 2023
To gain further insight into these trends, TechTarget’s Enterprise Strategy Group (ESG) surveyed 393 IT and cybersecurity professionals at organizations in North America (US and Canada) responsible for evaluating or purchasing cloud security technology products and services.


2023 Global Cloud Threat Report
The 2023 Global Cloud Threat Report exposes the latest security threats to public clouds, containers, Kubernetes, and cloud-native apps, based on extensive research by the Sysdig Threat Research Team (TRT).
Videos

Detecting Threats to Kubernetes, Containers, and Google Cloud
See how Sysdig helps secure and accelerate innovation with Google Cloud.

Secure DevOps Practices at Yahoo Japan
With more than 3,000 developers and a large Kubernetes environment, learn how Yahoo Japan is preventing cyber-attacks and unauthorized access by introducing appropriate security measures for the container environment.

Securing and Monitoring AWS Container Services
Developers, operations, and security teams must work together to address key workflows to secure and monitor containers, Kubernetes and cloud services across...
Webinars
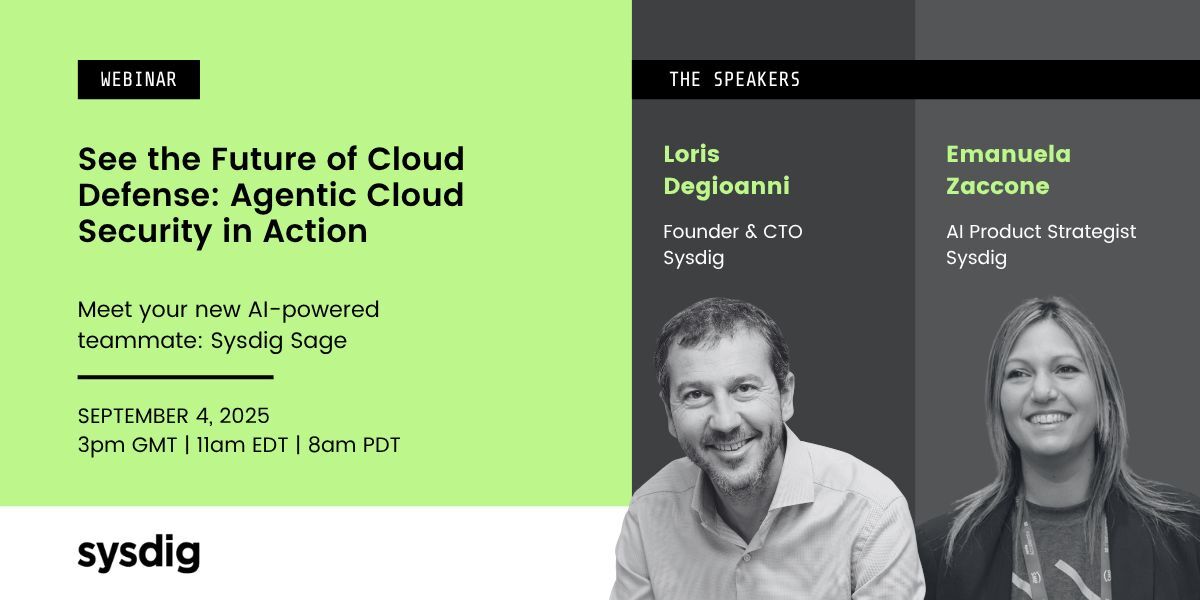
See the Future of Cloud Defense: Agentic Cloud Security in Action
.png)
Break the Bot: The Ultimate AI Challenge
Join us Aug 13 for an exclusive, hands-on demonstration of Sysdig's latest AI security innovations. Our new demo, Break the Bot: The Ultimate AI Challenge, gives you a front-row seat to the real-world risks AI introduces—and how Sysdig stops attackers in their tracks.
.png)
Packets, Pods & Prompts: Why Open Source is the Future of Cloud Security
Join this exclusive conversation with three titans of open source—the minds behind Falco, Wireshark, and Kubernetes—as they explore why open-source models are not just resilient, but essential to the next wave of cloud security.
Events
Whitepapers

Securing AI: Navigating a New Frontier of Security Risk
Organizations worldwide are turning to artificial intelligence (AI) to gain insights, optimize operations, and remain competitive in an increasingly digitized economy. As businesses move workloads to cloud‑native environments to support these AI initiatives, they encounter a new frontier of security risk. For security managers building cloud security programs, it’s crucial to take a step back and ask: Does your current program truly cover the unique risks AI workloads bring?

The 555 Guide for Cloud Security Practitioners
The Sysdig 555 Benchmark for Cloud Detection and Response sets the standard for operating securely in the cloud, emphasizing the need for security teams to detect, triage, and respond to attacks within the average time it takes threat actors to conduct them: 10minutes.