What is the shared responsibility model for cloud security?
Understanding your organization’s role versus the cloud service provider’s role regarding who protects data, applications, infrastructure, and more is critical before migrating resources into the cloud.
Shared responsibility model definition
The shared responsibility model is a security and compliance framework that outlines everything a cloud service provider (CSP), such as Amazon AWS, Microsoft Azure, or Google Cloud, is responsible for and what customers need to secure themselves.
This model enables CSPs and customers to understand what they must account for and reduces the chance of visibility gaps. This also means that if either side fails in its cloud security duties, data breaches can happen.
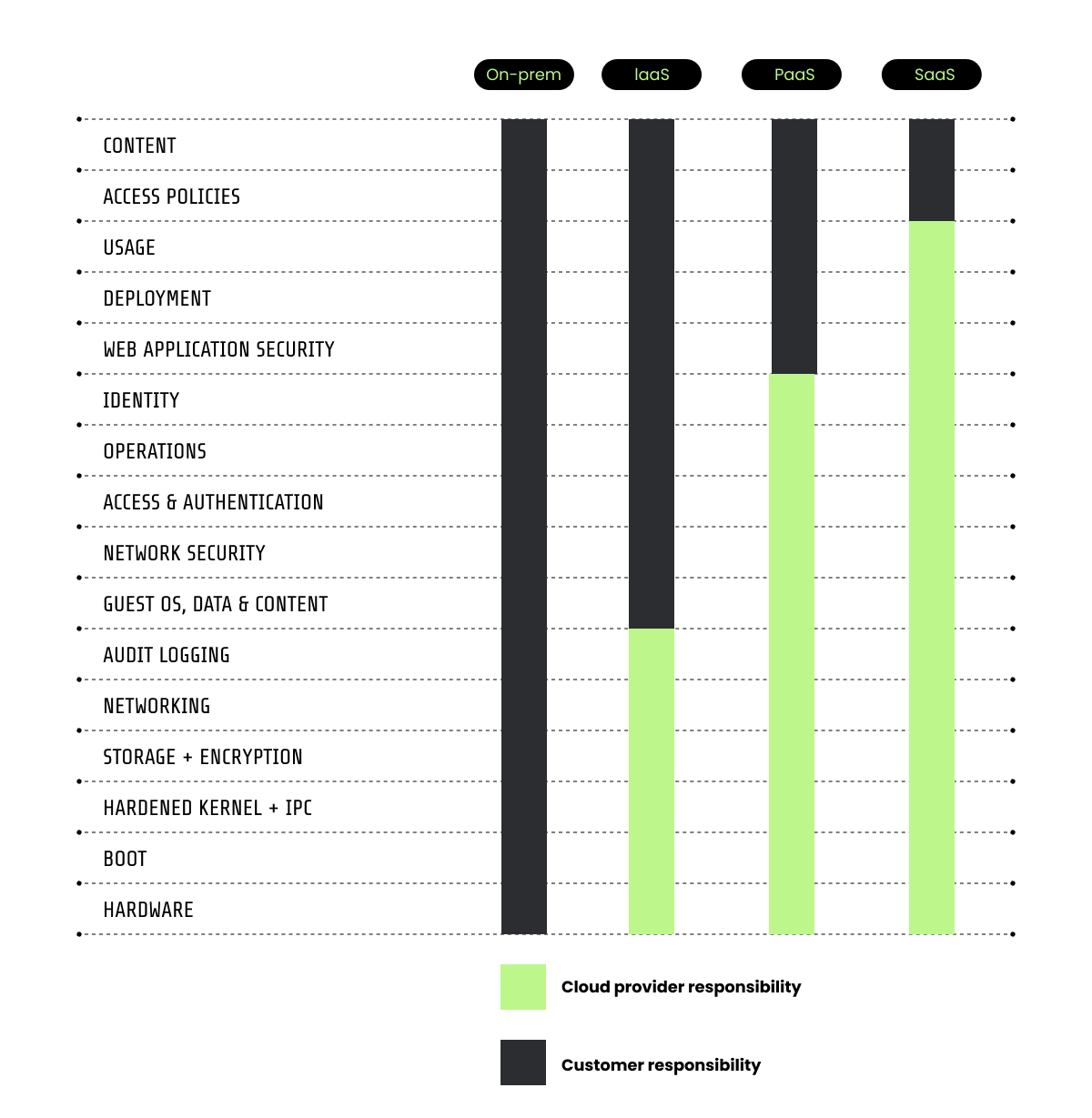
CSPs handle security of the cloud (e.g., cloud infrastructure), while customers manage security in the cloud (e.g., data, endpoints, identities, and applications). The exact delegation of duties between the two parties will depend on the cloud deployment, whether it’s infrastructure as a service (IaaS), platform as a service (PaaS), or software as a service (SaaS).
When all data, applications, and infrastructure were limited to on-premises deployments, the customer assumed responsibility for all of it. Everything could be secured behind the traditional security perimeter and there was no potential confusion regarding security responsibilities.
Now, more and more companies are migrating their resources and applications into the cloud to reduce the reliance on physical infrastructure, remotely access data and applications, lower IT costs, and scale more effectively. And security responsibility becomes confused.
Why the shared responsibility model exists
A common misconception arose because while customers manage everything for on-prem deployments, they don’t own or manage the infrastructure in the cloud. CSPs offered security capabilities and customers became unsure who truly managed security for what.
The shared responsibility model helps provide clarity on cloud security responsibility. Security becomes shared, with different aspects handled by the CSP while the customer handles others.
The cloud shared responsibility model provides several benefits, including:
- Reduced IT burden: CSPs provide and secure the cloud infrastructure, trimming IT costs for customers.
- Improved compliance and security posture: CSPs often provide advanced security capabilities, which can help customers with smaller security budgets keep their assets secure in the cloud and meet compliance requirements.
- Transparent accountability: CSPs are clear on what they secure, leaving customers aware of where their responsibility for protecting their resources and applications exists.
The shared responsibility model isn’t without challenges, including:
- Increased complexity: Determining how to meet their responsibility can result in more security and compliance complexity for customers. This is especially true for multi-cloud or hybrid cloud environments, where different cloud deployments and CSPs can create confusion about the customer’s security needs.
- Difficult risk remediation: Customers rely on CSPs to patch vulnerabilities and manage other cloud security risks related to infrastructure, which can leave the former potentially vulnerable if the CSP fails to act quickly.
Responsibilities between service provider and customer
As mentioned above, the CSP is generally responsible for security of the cloud, while the customer handles securing everything in the cloud.
How this breaks down between the two parties often looks like:
Cloud service provider responsibilities
CSPs provide security for aspects of cloud computing they control, including:
- Physical data centers, such as hardware, facilities, and networking.
- Infrastructure, such as servers, storage, and virtualization layer.
- Cloud service availability and redundancy.
- Managed services, which will depend on service type.
Customer responsibilities
The customer typically focuses on data security because the CSP lacks visibility into what’s hosted on its servers. Other areas include:
- Identity and access management (IAM), such as protecting credentials and secrets management.
- Data protection, such as encryption, classification, and authorization.
- Application, operating system, and endpoint security.
- Configuration of firewall and other security tools.
For example:
- AWS shared responsibility model involves AWS securing the infrastructure of all AWS Cloud services.
- Azure shared responsibility model has Microsoft sharing some IAM, application, and network controls depending on cloud deployment.
- Google Cloud shared responsibility model follows the traditional delegation between them and customers.
Shared responsibility across service models
When considering a cloud service model, organizations need to understand how cloud security is split between them and the CSP. The choices for cloud deployment are usually between IaaS, PaaS, and SaaS.
Infrastructure as a service (IaaS)
IaaS is a cloud computing model where the customer pays for access to cloud infrastructure, such as Google Cloud Compute Engine.
For IaaS deployments, the customer bears the most responsibility for their cloud assets and environments. The customer needs to account for data security; application and endpoint security; access and authentication; network security; and guest OS, data, and apps.
The CSP will most often be responsible for infrastructure and storage, which includes hardware security, data center security, data storage, and virtualization and server usage.
Platform as a service (PaaS)
PaaS is a cloud computing model where the customer pays for a platform on which they can build, manage, and deploy applications, such as Google Kubernetes Engine and Azure App Service.
A PaaS deployment involves more responsibility shifting to the CSP rather than the customer. CSPs provide network security; audit logging; guest OS, data, and content; storage; and hardware. The customer focuses on data security, code security, and application deployment and security.
With PaaS, the CSP and customer can sometimes share responsibilities. For example, with Azure, customers and Microsoft share responsibilities for identity and directory infrastructure, applications, and network.
Software as a service (SaaS)
SaaS is a cloud computing model where customers pay a subscription to access applications via web browser instead of on local machines, like Microsoft 365 and Google Workspace.
For SaaS deployments, the CSP or vendor provides the majority of the responsibilities, such as application, network, and hardware security. The customer focuses on workload and data security and access policies.
Key best practices for the shared responsibility model
- Understand your cloud deployment and responsibilities: Learn about your cloud deployment and review the service-level agreement (SLA) to determine what you and your CSP are responsible for to ensure there are no visibility gaps.
- Ensure data security: The customer remains in charge of securing their data and anything developed or created on the CSP's infrastructure, no matter the cloud deployment.
- Implement strong IAM: Adopt IAM controls to protect your data in the cloud, such as role-based access (RBAC), least privilege, and multi-factor authentication (MFA). You can secure identity in the cloud with traditional IAM tools, with some limitations, or a cloud infrastructure and entitlement management (CIEM) solution.
- Stay atop patch and vulnerability management: Perform continuous patching and vulnerability management to eliminate cloud risks that could actually impact your production environments.
- Shift left security: Adopt DevSecOps to implement a secure software development lifecycle. This includes infrastructure as code (IaC) to detect configuration drift and policy-as-code to manage infrastructure policies and rules.
- Use continuous monitoring and threat detection tools: Implement a cloud-native application protection platform (CNAPP) to get deep visibility into your cloud deployment, ensure you detect threats in real time, and get risk contextualization. Adopt cloud security posture management (CSPM) to detect misconfigurations and compliance violations.
- Consider managed services: Look into using managed security services if your budget cannot adequately protect your parts of the shared responsibility model.
With these shared responsibility model best practices, you can better manage common misconfigurations that lead to data exposure, remedy poor IAM, discover unpatched vulnerabilities, and have visibility across your cloud environments.
Get comprehensive cloud security with Sysdig Secure
Sysdig Secure is a runtime-first CNAPP that helps you identify and prioritize real security risks and threats, respond in real time, and get deep visibility into where data lives.
With Sysdig runtime insights, you get context into events, threats, and vulnerabilities to understand the risk each poses for your organization.
%201.svg)


