実績あるコンテナセキュリティの専門知識で重要な資産を保護
オンプレミス/エアギャップ/プライベートクラウドのコンテナセキュリティ
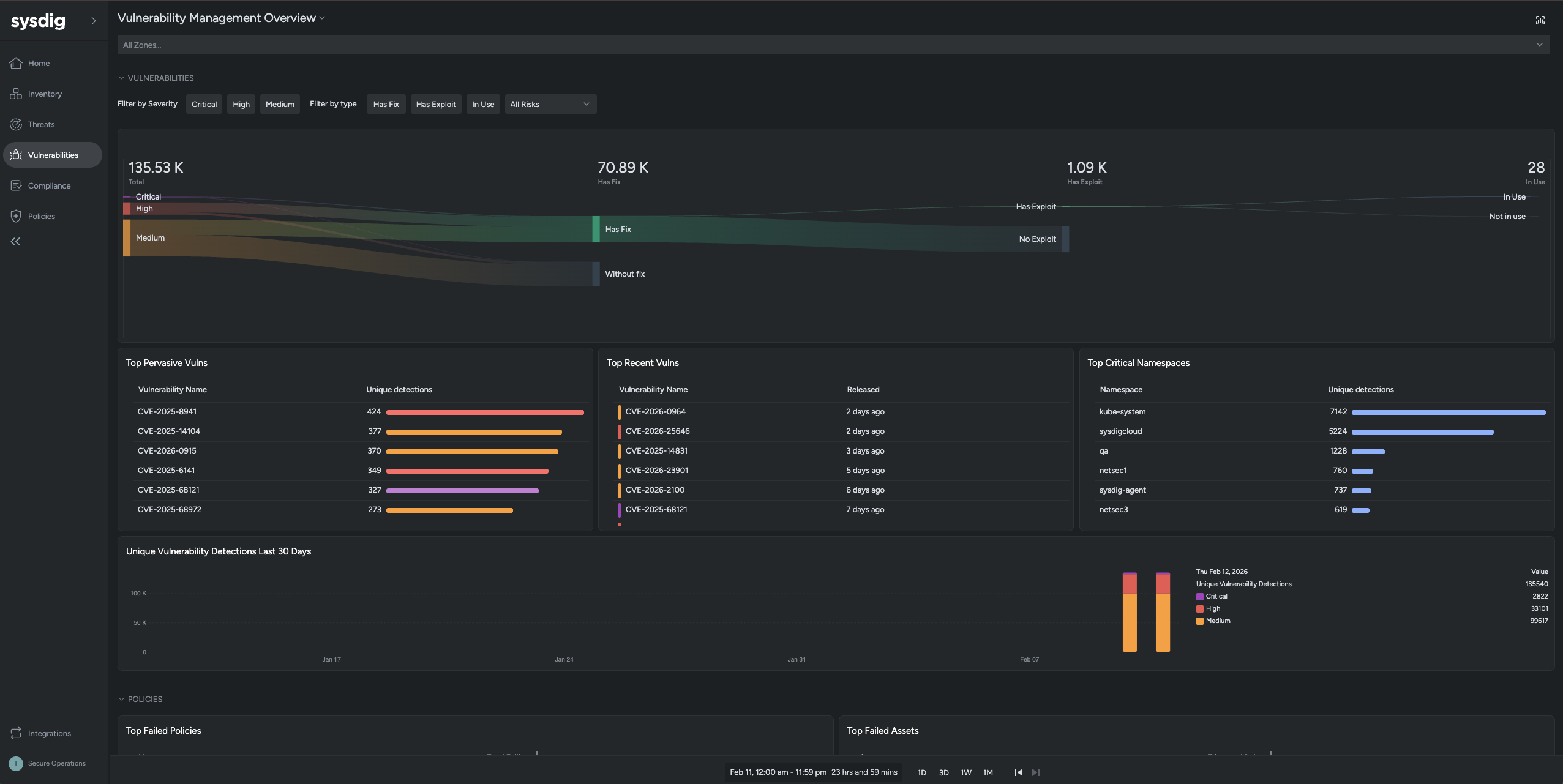
脆弱性管理
コンテナレジストリおよびCI/CDパイプラインのスキャンをランタイムコンテキストと組み合わせることで、完全な可視性と継続的な保護を実現
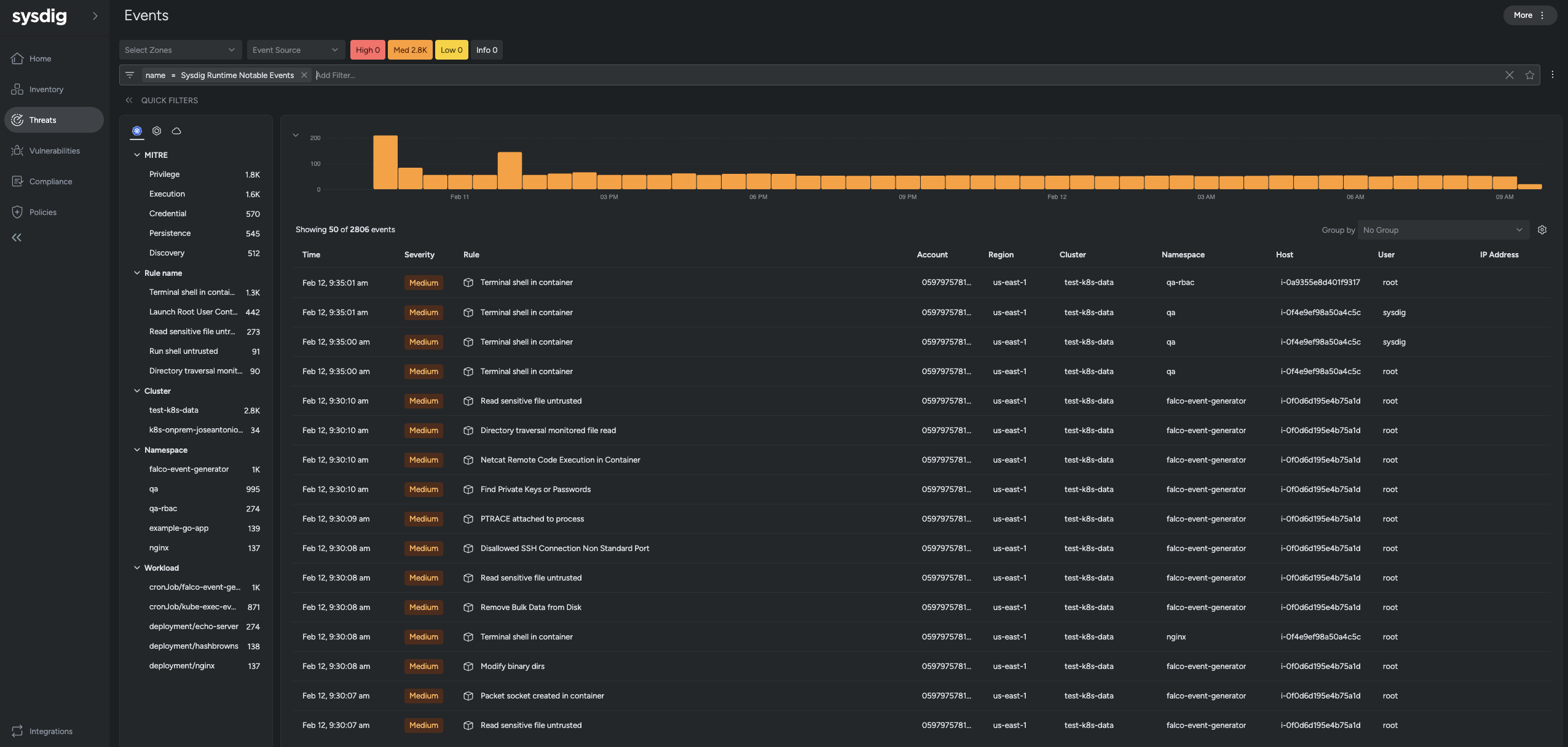
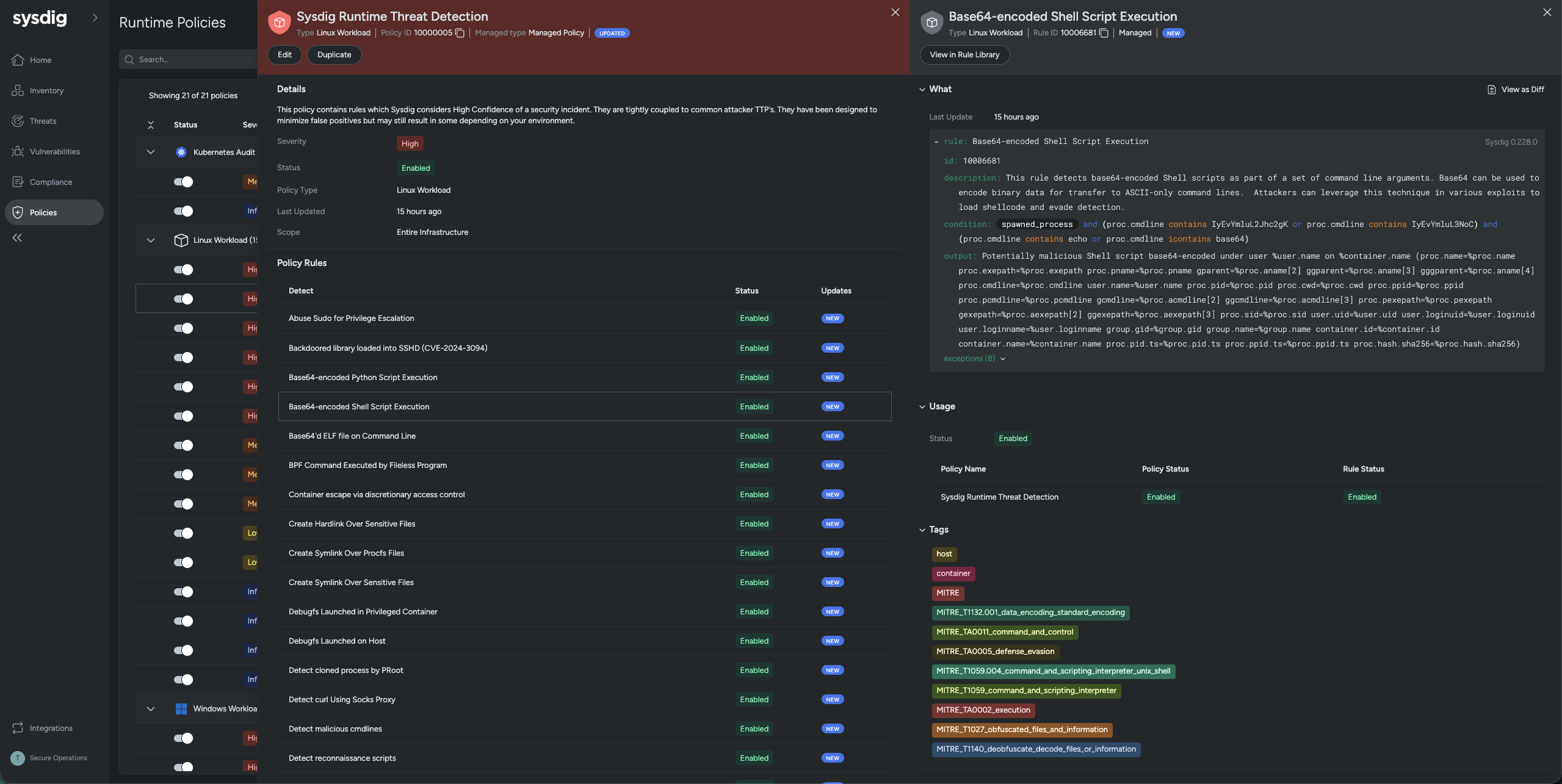
ランタイム脅威検知
Kubernetes、コンテナ、ホスト全体でランタイムの脅威を即座に検知し、実際に使用中の緊急リスクとノイズを区別
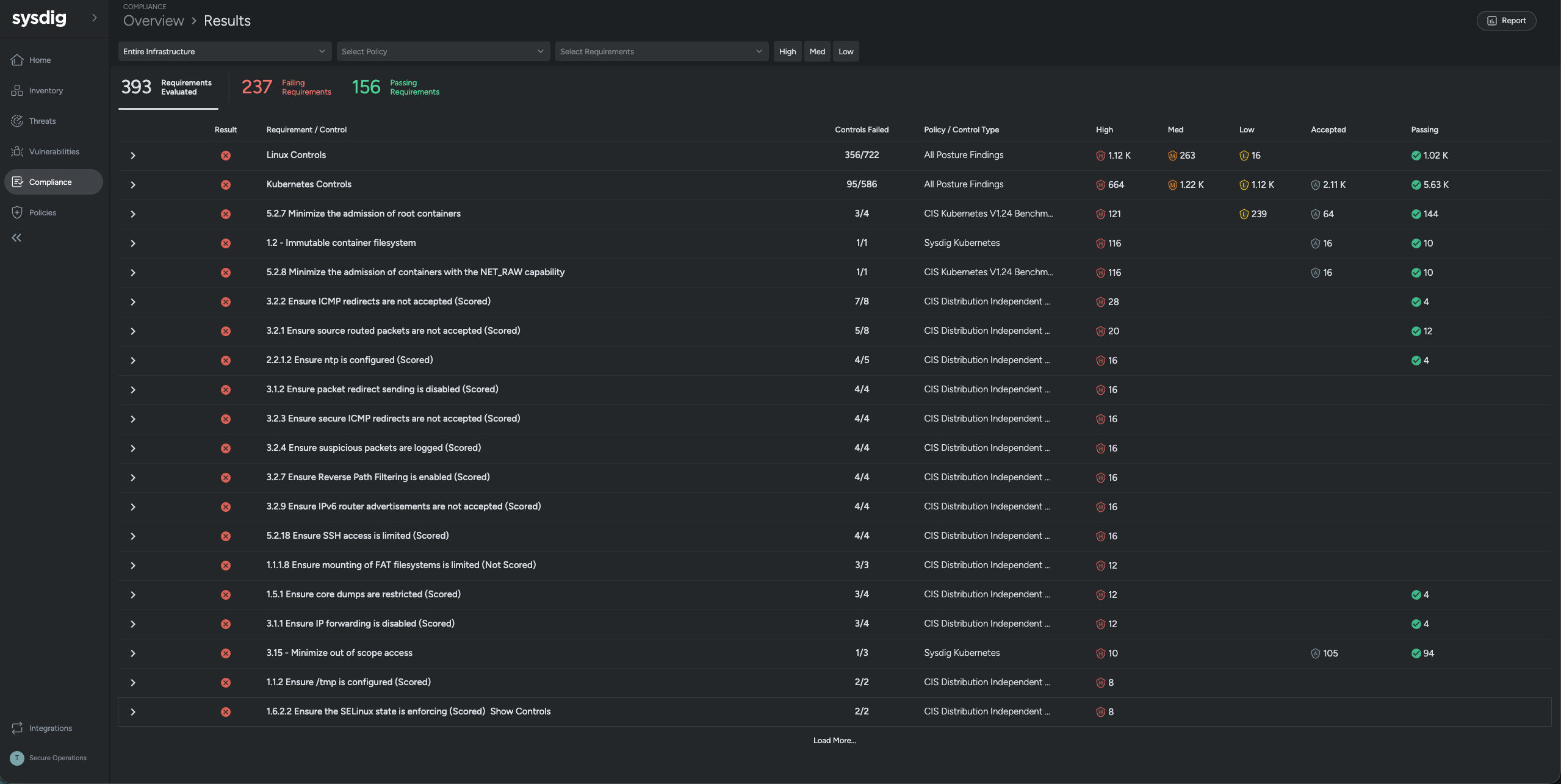
コンプライアンスとセキュリティポスチャ
組織や規制のフレームワーク(CIS Kubernetesベンチマーク、PCI-DSS、NIST、ISO27001など)に準拠するため、セキュリティ体制を監視・管理
インシデント対応とフォレンジック
システムコールのキャプチャとフォレンジック再構築により、不審なアクティビティを迅速かつ確実に特定・調査・対応
Sysdigにより、これまで以上に迅速に、より強固で監査対応可能なコンプライアンスを実現できました。
オンプレミスおよびプライベートクラウド向けランタイムセキュリティ
複雑なオンプレミスおよびプライベートクラウド環境において、Kubernetes、コンテナ、ホストを保護するには、専門的なアプローチが求められます。Sysdigは、実績に裏付けられたコンテナセキュリティの専門知識により、こうした特有の課題への対応を支援します。
Sysdigは、SaaSおよびバックエンドコンポーネントを自社で管理できるセルフマネージドモデルなど、柔軟な導入オプションを提供しています。また、エアギャップ環境での導入にも対応しています。Sysdigを利用することで、すべてのワークロードデータ、セキュリティデータ、テレメトリはお客様の環境内に保持され、データ主権に関する社内ポリシーや外部規制への準拠を実現できます。
さらにSysdigは、kOps、OpenShift 4、EKS、GKE、AKS、IKS、ROKS、RKE2など、さまざまなKubernetesディストリビューションとの継続的な互換性を確保しています。加えて、主要なSIEM、SOAR、チケッティングプラットフォームとシームレスに統合し、重要なランタイムおよびフォレンジックのコンテキストを付加します。