Browse all content by asset type.
Forrester names Sysdig a Leader in CNAPP

DEFENSE REPORT
AI Helps Teams Reduce MTTR by 76%
Sysdig named representative vendor in Gartner Market Guide for CNAPP
Blog Posts

TeamPCP expands: Supply chain compromise spreads from Trivy to Checkmarx GitHub Actions

AI coding agents are running on your machines — Do you know what they're doing?
Runtime security for AI coding agents: Protecting AI-assisted development
Briefs
The Business Value of Agentic AI for Cloud Security
Learn how agentic AI and Sysdig Sage™ combine human expertise with automation to accelerate cloud threat detection, streamline response, and cut security costs.

Sysdig Corporate Brief
Founded by the creators of open source standards — Falco, Stratoshark, and Wireshark — and built on agentic AI, Sysdig delivers real-time cloud defense grounded in the uncompromising truth of runtime.
BRIEF. 2025 Cloud‐Native Security and Usage Report
This is a special edition of Sysdig’s 2025 Cloud-Native Security and Usage Report, providing only the usage and analysis of the open source detection tool, Falco.
Case Studies
.png)
Global infrastructure provider cuts SOC 2 audit work by 80%
A global infrastructure provider automated SOC 2 compliance, improved runtime visibility, and eliminated weeks of manual audit work with Sysdig Secure.
.png)
Global technology leader gains unified visibility across 5 PB of data
Global Technology Leader unifies cloud monitoring to eliminate blind spots and outages

Partior cuts alert noise 57% with Sysdig Sage™
Partior saves 30+ hours a month with AI-powered runtime visibility
Ebooks
Top 6 Use Cases for Monitoring Cloud-Native Workloads with Sysdig Monitor
Securing the Cloud: The Benefits of Falco with an Enterprise Experience
An ebook with 3 mini case studies heavily featuring Falco and how it works with Sysdig, plus a callout to Falco Feeds at the end.
Blueprints
Your Blueprint to Agentic Cloud Security, the Right Way
This blueprint captures what agentic cloud security done right looks like for the future: proactive, contextual, and human-centered. It reveals how AI that reasons, plans, and acts can help defenders move with precision and confidence in the cloud.
Drowning in Alerts? Here’s the Blueprint to Take Control of Vulnerability Management.
Learn how to prioritize risk in real time, unify visibility across environments, and automate remediation to stay secure without slowing innovation.
Your Blueprint to Cloud Security, the Right Way
This blueprint defines what cloud security, the right way, looks like for the decade ahead: fast, open, and intelligent. It’s a manifesto for how modern security teams can win in the AI era.
Guides
Cloud Security for Google Cloud
This guide outlines key requirements and capabilities for establishing comprehensive security for Google Cloud services and containers.
Cloud Security for Amazon Web Services
This guide outlines key requirements and capabilities for establishing comprehensive security for AWS cloud services and containers.
Secure Your Cloud in Minutes - Your Checklist for Meeting the 555 Benchmark
Sysdig’s 555 Benchmark for Cloud Detection and Response offers a standard to use when measuring how fast your security teams can counter attackers. Specifically, the benchmark finds that to outpace attacks, your security teams need to detect threats within 5 seconds, correlate and triage data within the first 5 minutes, and initiate a tactical response within the next 5 minutes.Sysdig’s 555 Benchmark for Cloud Detection and Response offers a standard to use when measuring how fast your security teams can counter attackers. Specifically, the benchmark finds that to outpace attacks, your security teams need to detect threats within 5 seconds, correlate and triage data within the first 5 minutes, and initiate a tactical response within the next 5 minutes.
Infographics


The Evolution of Modern Cloud Security
Remember asking your teachers why you needed to know history? They probably said that learning history is important in understanding how society has changed and progressed over time, and that we can learn from past experiences and mistakes.


The Grand Atlas of Software Security
This infographic demonstrates how to secure each stage of the software lifecycle, with a focus on the Shift Left approach, where early remediation reduces risks and costs.
Podcasts

"Screaming in the Cloud - August 3, 2023: Exposing The Latest Cloud Threats"
"Corey is joined by Anna Belak, Director, Office of Cybersecurity Strategy at Sysdig, to discuss the 2023 Global Cloud Threat Report."

Screaming in the Cloud Podcast : Making Sense of Data
"Screaming in the Cloud host Corey Quinn was recently joined by Harry Perks, Principal Product Manager at Sysdig to discuss challenges in the observability space."

Screaming in the Cloud Podcast
"Corey is joined by Michael Clark, Director of Threat Research at Sysdig, to discuss the refreshingly non-salesy approach of the 2022 Sysdig Cloud-Native Threat Report."
Press Releases

Sysdig Launches Runtime Security for AI Coding Agents
Sysdig, the leader in real-time AI-powered cloud defense, today announced runtime security for AI coding agents, enabling organizations to safely adopt autonomous development tools.

Sysdig Celebrates 10 Years of Falco with $70,000 Donation
Sysdig, the leader in real-time AI-powered cloud defense, today announced a $70,000 donation to the Falco project through the Linux Foundation’s crowdfunding initiative.
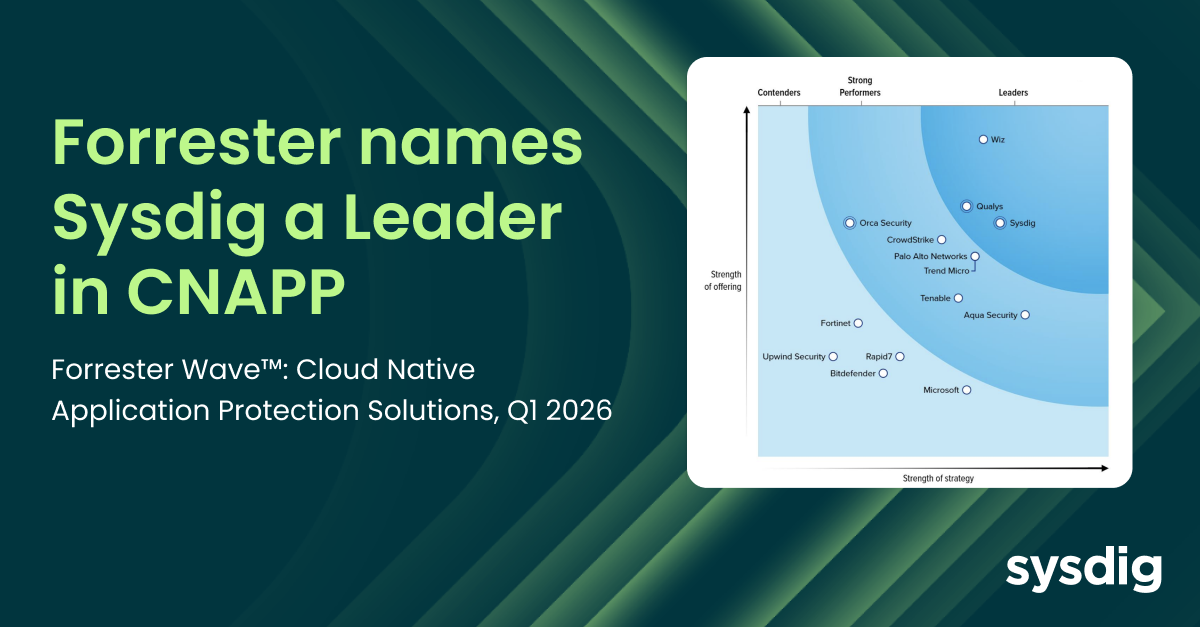
Sysdig Named a Leader in CNAPP as Runtime Redefines Cloud Security in 2026
Sysdig today announced that it has been named a Leader in “The Forrester Wave™: Cloud Native Application Protection Solutions, Q1 2026” report, earning the distinction alongside just two other companies.
Reports


Latio Tech 2025 Cloud Security Market Report
The 2025 Latio Cloud Security Market Report examines the technologies and strategies shaping the next generation of cloud and AI defense. As organizations adopt AI workloads and distributed architectures, the traditional boundaries of security continue to dissolve. Latio’s analysis highlights how the market is shifting from visibility to real-time, runtime protection—and why this evolution is critical to managing machine-speed risk. Within the report, Latio names Sysdig a leader for its ability to deliver the depth of telemetry, customization, and AI-driven correlation security teams need to operationalize cloud incident-response programs. By combining open innovation with deep runtime visibility, Sysdig helps organizations detect, prioritize, and respond to threats faster—across hybrid and AI-powered environments. This report serves as the most comprehensive guide for security leaders looking to understand where the market is headed, what capabilities define the leaders, and how to prepare their organizations for the future of cloud and AI security.

2025 Cloud Defense Report
Cloud attacks are accelerating, vulnerabilities are multiplying, and AI is reshaping both the attack surface and expectations for defense. In 2025, security leaders face a defining paradox: embracing AI to innovate and protect, while defending against the very AI-powered threats that evolve in seconds. The future of security lies in real-time, context-aware defense—rooted in visibility, collaboration, and AI that empowers defenders to move as fast as attackers.

Sysdig 2024 Cloud-Native Security and Usage Report
Videos

Detecting Threats to Kubernetes, Containers, and Google Cloud
See how Sysdig helps secure and accelerate innovation with Google Cloud.

Secure DevOps Practices at Yahoo Japan
With more than 3,000 developers and a large Kubernetes environment, learn how Yahoo Japan is preventing cyber-attacks and unauthorized access by introducing appropriate security measures for the container environment.

Securing and Monitoring AWS Container Services
Developers, operations, and security teams must work together to address key workflows to secure and monitor containers, Kubernetes and cloud services across...
Webinars

Lessons from the Trenches: Maintaining Effective Security in Cloud
ICG Consulting provides cloud hosting and managed security services for their financial back-office solution customers who want to deploy ICG’s applications without the usual headaches of complex cloud infrastructure.

Shift Cloud Security Left and Right with CNAPP, Powered by Runtime Insights - EMEA
To increase profitability in today’s business landscape, cloud-native applications deploy code on a continuous basis. However, conventional security methods are ill-suited for these environments as they operate independently and lack the ability to exchange information.
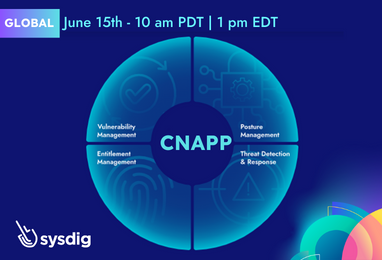
Shift Cloud Security Left and Right with CNAPP, Powered by Runtime Insights
Learn how to keep your security and DevOps teams shipping more secure applications by shifting security left and shielding right. Understand why real-time cloud detection and response across workloads, cloud services, and identities provides a fundamental CNAPP pillar to stop attacks and prevent breaches.
Events
Whitepapers
.png)

Securing AI: Navigating a New Frontier of Security Risk
Organizations worldwide are turning to artificial intelligence (AI) to gain insights, optimize operations, and remain competitive in an increasingly digitized economy. As businesses move workloads to cloud‑native environments to support these AI initiatives, they encounter a new frontier of security risk. For security managers building cloud security programs, it’s crucial to take a step back and ask: Does your current program truly cover the unique risks AI workloads bring?

The 555 Guide for Cloud Security Practitioners
The Sysdig 555 Benchmark for Cloud Detection and Response sets the standard for operating securely in the cloud, emphasizing the need for security teams to detect, triage, and respond to attacks within the average time it takes threat actors to conduct them: 10minutes.

.png)
.png)
.png)